Which of the following BEST describes the type of attack that is occurring? (Choose two.)

A.
DNS spoofing
B.
Man-in-the-middle
C.
Backdoor
D.
Replay
E.
ARP attack
F.
Spear phishing
G.
Xmas attack
Explanation:
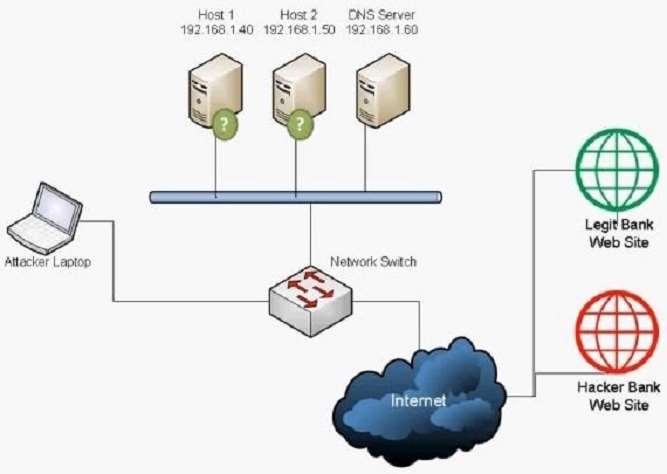
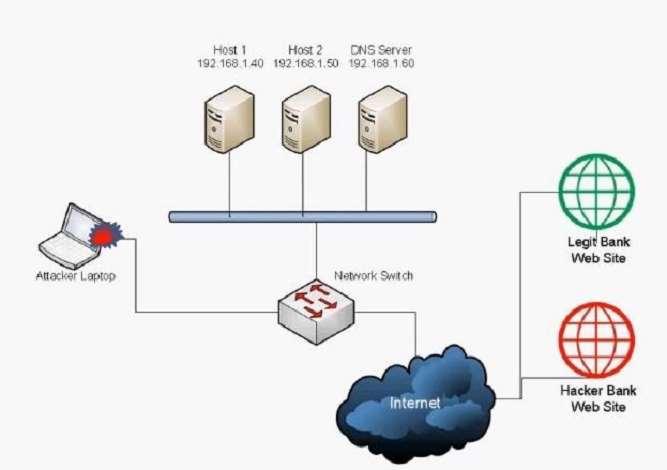
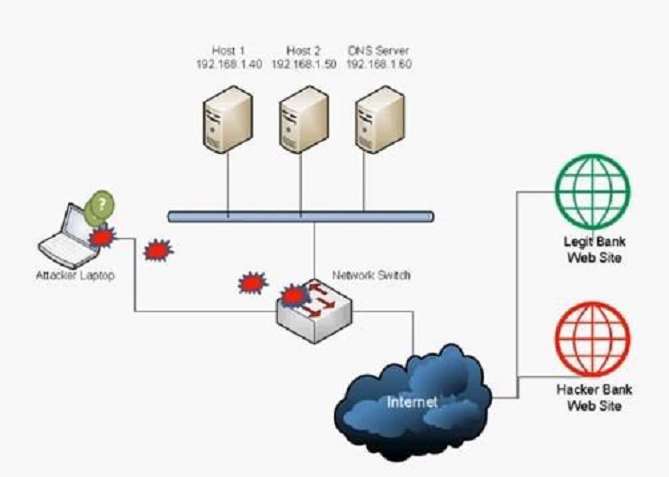
We have a legit bank website and a hacker bank website. The hacker has a laptop connected to the network.
The hacker is redirecting bank website users to the hacker bank website instead of the legit bank website. This
can be done using two methods: DNS Spoofing and ARP Attack (ARP Poisoning).
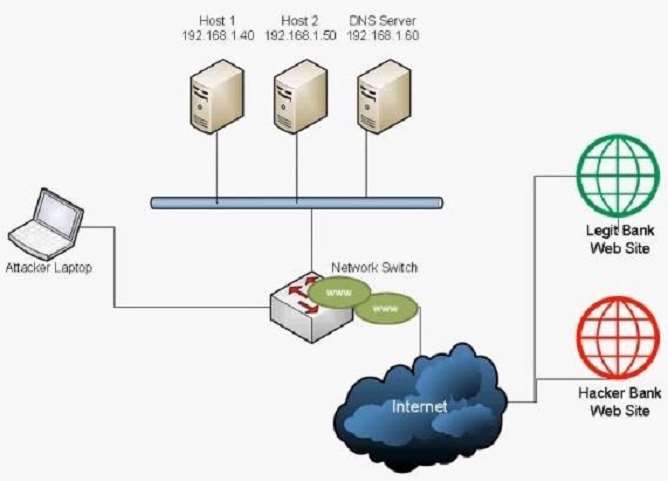
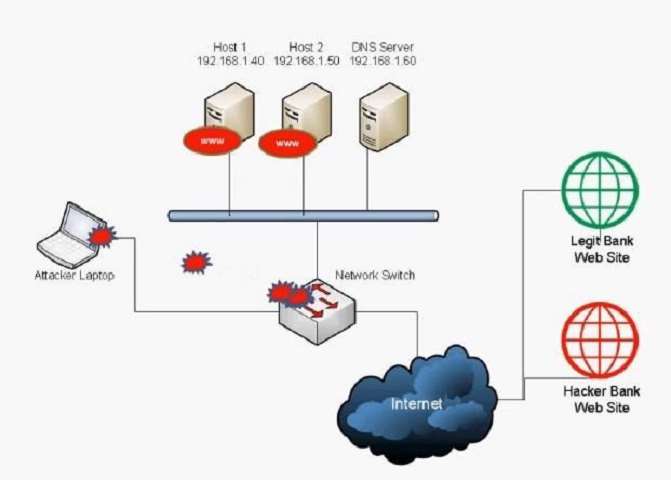
A: DNS spoofing (or DNS cache poisoning) is a computer hacking attack, whereby data is introduced into a
Domain Name System (DNS) resolver’s cache, causing the name server to return an incorrect IP address,
diverting traffic to the attacker’s computer (or any other computer).
A domain name system server translates a human-readable domain name (such as example.com) into a
numerical IP address that is used to route communications between nodes. Normally, if the server doesn’tknow a requested translation it will ask another server, and the process continues recursively. To increase
performance, a server will typically remember (cache) these translations for a certain amount of time, so that, if
it receives another request for the same translation, it can reply without having to ask the other server again.
When a DNS server has received a false translation and caches it for performance optimization, it is
considered poisoned, and it supplies the false data to clients. If a DNS server is poisoned, it may return an
incorrect IP address, diverting traffic to another computer (in this case, the hacker bank website server).
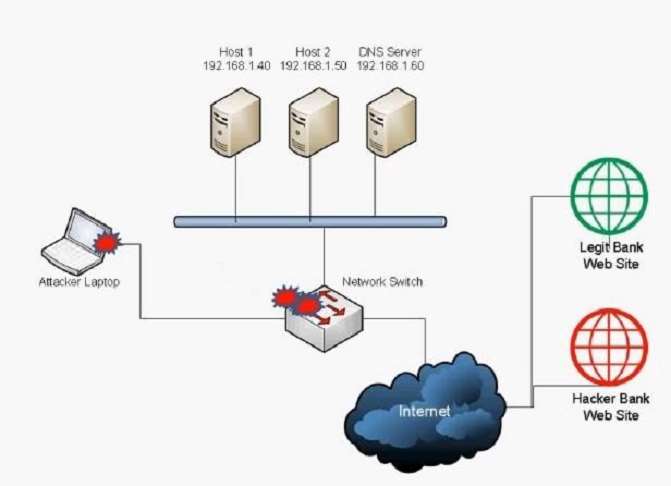
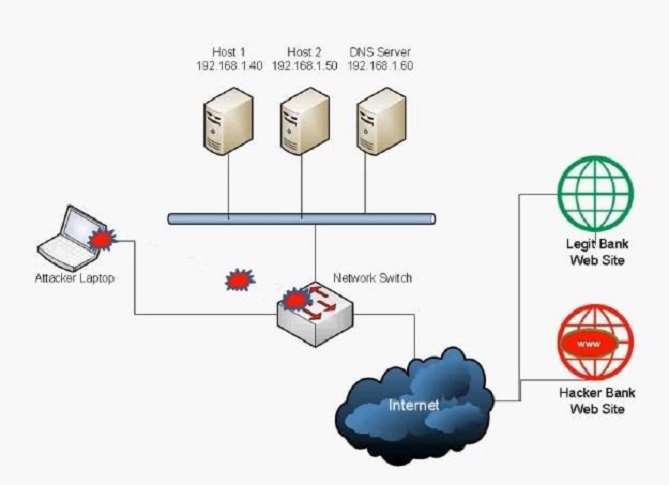
E: Address Resolution Protocol poisoning (ARP poisoning) is a form of attack in which an attacker changes the
Media Access Control (MAC) address and attacks an Ethernet LAN by changing the target computer’s ARP
cache with a forged ARP request and reply packets. This modifies the layer -Ethernet MAC address into the
hacker’s known MAC address to monitor it. Because the ARP replies are forged, the target computer
unintentionally sends the frames to the hacker’s computer first instead of sending it to the original destination.
As a result, both the user’s data and privacy are compromised. An effective ARP poisoning attempt is
undetectable to the user.
ARP poisoning is also known as ARP cache poisoning or ARP poison routing (APR).