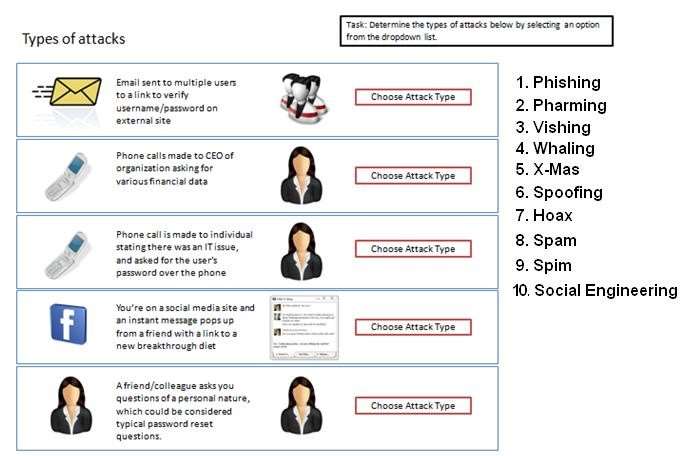
DRAG DROP
Determine the types of attacks below by selecting an option from the dropdown list.
Determine the types of Attacks from right to specific action.
Select and Place:

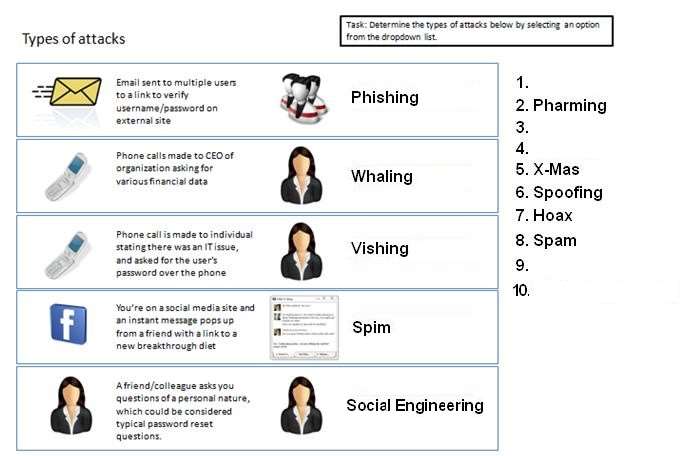
Explanation:
A: Phishing is the act of sending an email to a user falsely claiming to be an established legitimate enterprise in
an attempt to scam the user into surrendering private information that will be used for identity theft.
Phishing email will direct the user to visit a website where they are asked to update personal information, such
as a password, credit card, social security, or bank account numbers, that the legitimate organization already
has. The website, however, is bogus and set up only to steal the information the user enters on the page.
B: Whaling is a specific kind of malicious hacking within the more general category of phishing, which involves
hunting for data that can be used by the hacker. In general, phishing efforts are focused on collecting personal
data about users. In whaling, the targets are high-ranking bankers, executives or others in powerful positions or
job titles.
Hackers who engage in whaling often describe these efforts as “reeling in a big fish,” applying a familiar
metaphor to the process of scouring technologies for loopholes and opportunities for data theft. Those who are
engaged in whaling may, for example, hack into specific networks where these powerful individuals work or
store sensitive data. They may also set up keylogging or other malware on a work station associated with one
of these executives. There are many ways that hackers can pursue whaling, leading C-level or top-level
executives in business and government to stay vigilant about the possibility of cyber threats.
C: Vishing is the act of using the telephone in an attempt to scam the user into surrendering private information
that will be used for identity theft. The scammer usually pretends to be a legitimate business, and fools the
victim into thinking he or she will profit.
D: SPIM is a term sometimes used to refer to spam over IM (Instant Messaging). It’s also called just spam,
instant spam, or IM marketing. No matter what the name, it consists of unwanted messages transmitted
through some form of instant messaging service, which can include Short Message Service (SMS).E: Social engineering is a non-technical method of intrusion hackers use that relies heavily on human
interaction and often involves tricking people into breaking normal security procedures. It is one of the greatest
threats that organizations today encounter.
A social engineer runs what used to be called a “con game.” For example, a person using social engineering to
break into a computer network might try to gain the confidence of an authorized user and get them to reveal
information that compromises the network’s security. Social engineers often rely on the natural helpfulness of
people as well as on their weaknesses. They might, for example, call the authorized employee with some kind
of urgent problem that requires immediate network access. Appealing to vanity, appealing to authority,
appealing to greed, and old-fashioned eavesdropping are other typical social engineering techniques.http://www.webopedia.com/TERM/P/phishing.html
http://www.techopedia.com/definition/28643/whaling
http://www.webopedia.com/TERM/V/vishing.html
http://searchsecurity.techtarget.com/definition/social-engineering