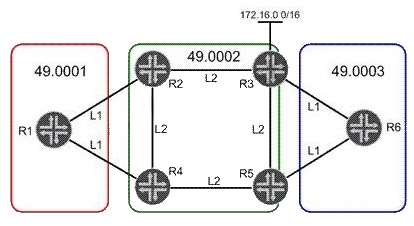
In the exhibit, network 172.16.0.0/16 is redistributed into IS-IS in Area 49.0002. R1 must use R2 to
access 172.16.0.0/16. All other traffic leaving Area 49.0001 must use R4.Which three steps will
accomplish this task? (Choose three.)

A.
Configure R1 to ignore the attached bit.
B.
Disable the attached bit on R4 in Area 49.0001.
C.
Enable an L2 adjacency on the link between R1 and R2.
D.
Leak network 172.16.0.0/16 into L1 on R2.
E.
Redistribute a static default route into L1 on R4.
Explanation:


L2 R1-R2??? Why? We already have 172.16/16 via leaking, so we only need default on R1 to R4 for any other traffic.
1
0
Agreed. But only in labs you would do this 🙂 .. If you don’t do ignore attached , there is probability it can traverse R2 if link to R4 is dead (as it will generate a def route as you referred).
I believe its weird options as you point out but given the options , those seem valid.
1
0
Correct answere is A D E
0
0
A,D,E correct answer
1
0
I believe that A,D,E are a correct answers.
1
0