Which of the following is NOT a valid VPN configuration option available in the VPN Manager of
the Simplified Rule Base?

A.
Point-to-Point
B.
Mesh
C.
Remote Access
D.
Star with Meshed Center
E.
Star
Explanation:
Creating the Simplified VPN Rules
C reating Simplified VPN rules is an oxymoron, because we’ve said
you don’t have to create any explicit encryption rules to make the VPN tunnels
happen with a VPN community. However, you do have to create a new
Simplified Policy and define access rules (unencrypted connections) and rules
that specify a VPN community in the If Via column with Accept as the action
(which forces this traffic through a VPN tunnel where it is encrypted). In the
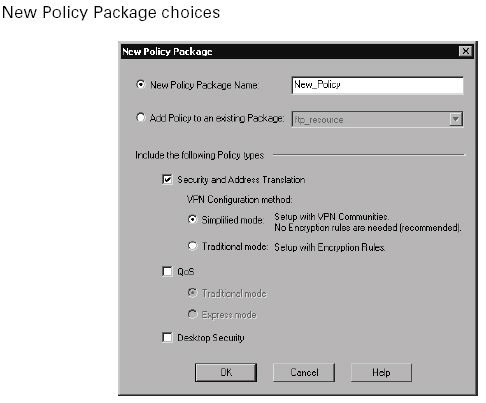
SmartDashboard, click on File _ New to display the New Policy Package window (Figure below).
Give the policy a name (remember, no spaces and no dashes) and select Security And Address Translation. This option reveals the VPN Configuration methods: You can choose to create a Traditional mode
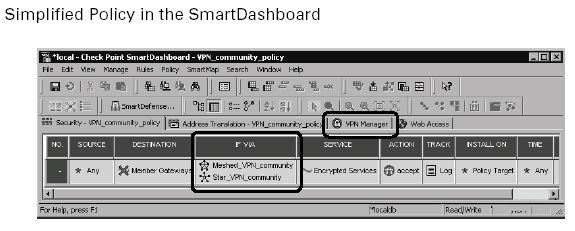
policy (you write the encryption rules) or a Simplified mode policy (no encryption rules are explicitly written; they are assumed based on your VPN community definitions). After selecting Simplfied Mode and clicking OK, the new Simplified Policy is now displayed in SmartDashboard. You can tell the difference between a Traditional mode policy and a Simplified mode policy by looking at the rule base. A Simplified Policy has a new column called If
Via and a new tab called VPN Manager, as well as an implied VPN rule, as shown in Figure below.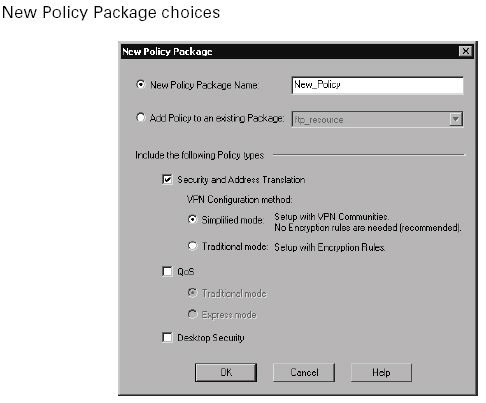
If you look at the options available in the Action column, you will also notice that the Encrypt options are gone. The If Via column is used to define access rules between VPN sites participating in a VPN community. If Via is not an acronym. It’s easier to understand if you “read” a rule: For example, a source of my network with a destination of another network going through (If Via) using HTTP is allowed (accepted). The addition of a VPN
community in the If Via column forces all traffic matching that rule to be encrypted/decrypted even
though the Action is Accept. Remember that rules created in the rule base with nothing defined in
the If Via column do not affect the VPN community. To see how the VPN is configured, click on the
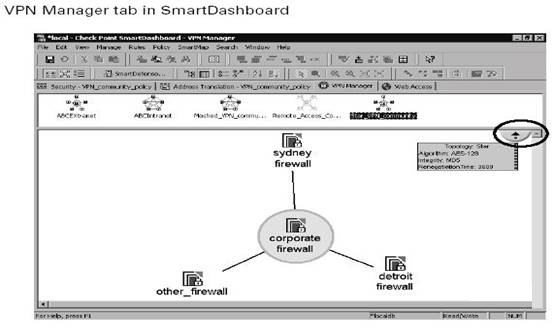
VPN Manager tab in the SmartDashboard to display your VPN communities, as shown in Figure below.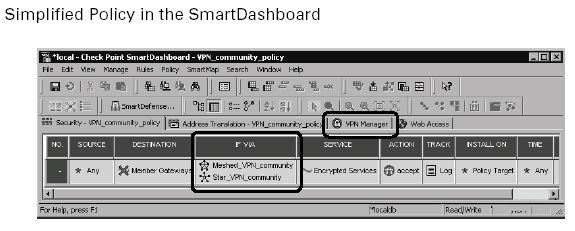
All VPN communities are listed here, including extranet management
(discussed in Chapter 8) and remote access VPNs (discussed in Chapters 9
and 10). Select the specific VPN community in the upper window of the VPN
Manager to display the topology of the VPN community in the lower pane. In
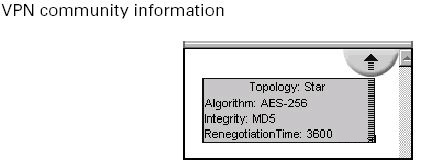
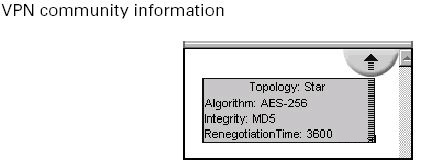
Figure above, selecting the circled portion of the picture will tell you all about
that VPN community: the type of topology (star, meshed, star/center-meshed),
the encryption algorithm, the data integrity method, and the key renegotiation
time as depicted in Figure below.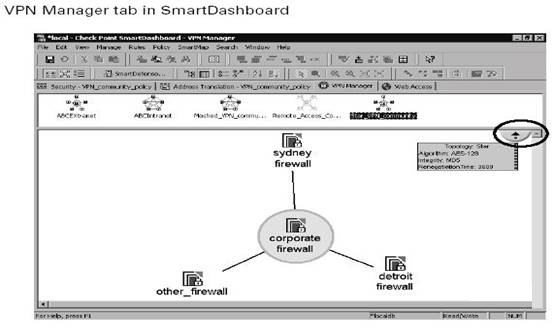
Aside from completing the access rules in the Security tab of the SmartDashboard and verifying/installing your policy, you’ve finished your Simplified VPN.
In Simplified mode (FP2), you could configure star and mesh intranet topologies
as well as remote access topologies, but you could not configure extranets.
Traditional mode was required in order to create extranet rules as well as
specific VPN rules. This is no longer true in FP3. Remote access, extranet, and
site-to-site Simplified VPNs can be configured in VPN communities