Which of the following includes all of these requirements?
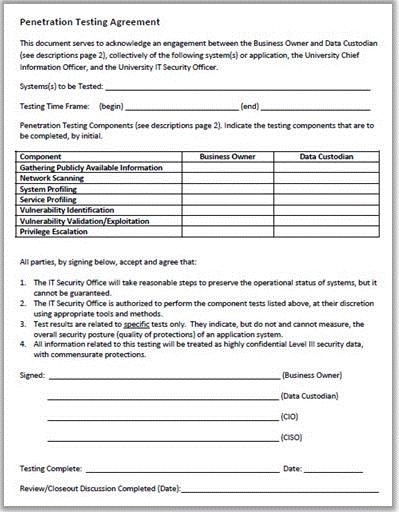
John, a penetration tester, was asked for a document that defines the project, specifies
goals, objectives, deadlines, the resources required, and the approach of the project. Which
of the following includes all of these requirements?
What query does he need to write to retrieve the information?
A WHERE clause in SQL specifies that a SQL Data Manipulation Language (DML)
statement should only affect rows that meet specified criteria. The criteria are expressed in
the form of predicates. WHERE clauses are not mandatory clauses of SQL DML statements,
but can be used to limit the number of rows affected by a SQL DML statement or returned by a query.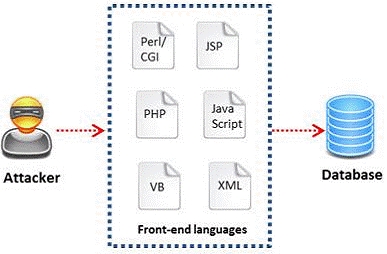
A pen tester is trying to gain access to a database by inserting exploited query statements
with a WHERE clause. The pen tester wants to retrieve all the entries from the database
using the WHERE clause from a particular table (e.g. StudentTable).
What query does he need to write to retrieve the information?
Which of the following types of penetration testing is performed with no prior knowledge of the site?
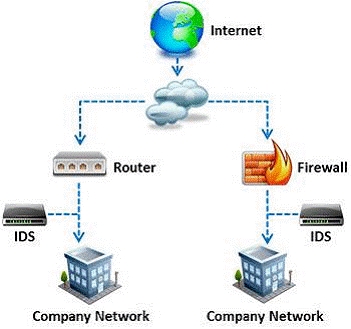
External penetration testing is a traditional approach to penetration testing and is more
focused on the servers, infrastructure and the underlying software comprising the target. It
involves a comprehensive analysis of publicly available information about the target, such as
Web servers, Mail servers, Firewalls, and Routers.
Which of the following types of penetration testing is performed with no prior knowledge of
the site?
What information can be collected by dumpster diving?
What information can be collected by dumpster diving?
which there is no proxy?
In which of the following firewalls are the incoming or outgoing packets blocked from
accessing services for which there is no proxy?
Which of the following policies helps secure data and protects the privacy of organizational information?
Which of the following policies helps secure data and protects the privacy of organizational
information?