Which of the following can you determine from only this entry?
Consider the following mail exchange entry:
hello.com IN MX 15mail1.hello.com
Which of the following can you determine from only this entry?
Which of the following is responsible for encrypting the data packets encapsulated in an SSLenabled HTTP sessi
Which of the following is responsible for encrypting the data packets encapsulated in an SSLenabled HTTP session?
The best way to thwart a dictionary attack is by enforcing a:
The best way to thwart a dictionary attack is by enforcing a:
Which of the following BEST utilizes OOAD artifacts to manage a project team?
Which of the following BEST utilizes OOAD artifacts to manage a project team? Divide the project
staff into:
Which is the default control type for an HTML input element?
Which is the default control type for an HTML input element?
Match the Java methods to the corresponding SQL data types
Mix and match
QUESTIONSQL Type Java Method
FLOAT
INTEGER
LONGVARBINARY
LONGVARCHAR
NUMERIC
OTHER
Java Method
getDouble(.
getInt(.
getBytes(.
getString(.
getBigDecimal(.
getObject(.
Match the Java methods to the corresponding SQL data types
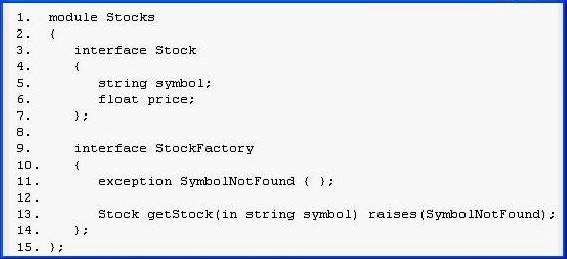
Which statement correctly describes this IDL definition?
Whose perspective should you take as you design the site?
Your new customer, Chattawa, is the education coordinator for Bluelake County Schools. He has
asked you to design a Web site to teach school personnel in aboriginal issues. He presents you
with a report about current concerns that aboriginal children’s learning styles are not being
addressed in the school system. He suggests that you reproduce the report online and add
aboriginal art in the margins. Whose perspective should you take as you design the site?
which types of relationships?
The creation of intermediate entities occurs during the logical database design phase for an
enterprise. It is used to resolve which types of relationships?
Which of the following is a messaging protocol designed to ensure the integrity of data sent between incompati
Which of the following is a messaging protocol designed to ensure the integrity of data sent
between incompatible computers?