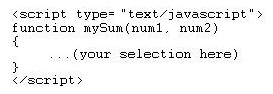
Which statement will correctly call a JavaScript function without error?
Which statement will correctly call a JavaScript function without error?
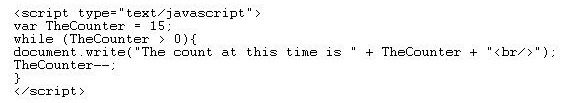
Which of the following will typically occur during this process?
An application is creating hashes of each file on an attached storage device. Which of the
following will typically occur during this process?
Which of the following would properly supply the sum of the two numbers?
Which of the following is the most effective response?
The chief operations officer (COO) has questioned the need for end-user training. Which of the
following is the most effective response?
Which term best describes this device?
You have been assigned to configure a DMZ that uses multiple firewall components. Specifically,
you must configure a router that will authoritatively monitor and, if necessary, block traffic. This
device will be the last one that inspects traffic before it passes to the internal network. Which term
best describes this device?
Which is the best technique to test a script for cross-browser compatibility?
Which is the best technique to test a script for cross-browser compatibility?
Which organization should you consult?
You want to learn more about a security breach that was recently discovered in a Windows server.
Which organization should you consult?
Which of the following techniques will best help reduce the severity of this attack?
A distributed denial-of-service (DDOS) attack has occurred where both ICMP and TCP packets
have crashed the company’s Web server. Which of the following techniques will best help reduce
the severity of this attack?
what is normalization?
With regard to databases, what is normalization?