Which of the following best describes this external style sheet?
You are creating a Web site for a customer. You will use an external linked style sheet for
controlling the style of elements and giving a consistent look and feel to the site. Which of the
following best describes this external style sheet?
Which of the following occurs in a relation when records are added or removed?
Which of the following occurs in a relation when records are added or removed?
which all the businesses in a particular market are involved in the same industry?
Which of the following market models is considered industry-centric that is, a model in which all
the businesses in a particular market are involved in the same industry?
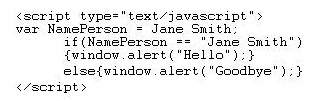
What is the expected result when you run this script in the browser?
which configuration scheme requires an address server to allocate an IP address to a client from a pool of add
In IPv6, which configuration scheme requires an address server to allocate an IP address to a
client from a pool of addresses?
Which of the following is a disadvantage of using GUI HTML editors?
Angel is using a GUI HTML editor to create a Web page that will be posted on the company site
during an advertising promotion. Which of the following is a disadvantage of using GUI HTML
editors?
Which of the following choices is the best step to resolve the bottleneck?
You are a site administrator who has identified a bottleneck on a small site. You find that
the processor is overburdened, the RAM is too small and NIC is approaching 100%
capacity. You are also considering installing a second virtual server. Which of the
following choices is the best step to resolve the bottleneck?
Which type of encryption is this application most likely to use to achieve this goal?
A packet is being sent from one computer to the next. This packet is being processed by an
application designed to encrypt sensitive data. One of the duties of this application is to ensure
that a packet has not been altered by an intruder. Which type of encryption is this application most
likely to use to achieve this goal?
Which of the following will accomplish this goal?
You want to create a quick solution that allows you to obtain real-time login information for the
administrative account on an LDAP server that you feel may become a target. Which of the
following will accomplish this goal?
What OOAD artifacts potentially need to be updated?
During implementation, the design is refactored to improve reuse and achieve more effective
placement of responsibilities. This refactoring results in a public method being moved from one
class to another. What OOAD artifacts potentially need to be updated?