Fill in the blank: The _________ collects logs and send…
Fill in the blank: The _________ collects logs and sends them to the _________ .
Which default user has full read/write access?
Which default user has full read/write access?
Fill in the blank: Browser-based Authentication sends u…
Fill in the blank: Browser-based Authentication sends users to a web page to acquire identities using ________
Which CLISH commands are required to be able to change …
What does the “unknown” SIC status shown on SmartConsol…
What does the “unknown” SIC status shown on SmartConsole mean?
What are the three conflict resolution rules in the Thr…
What are the three conflict resolution rules in the Threat Prevention Policy Layers?
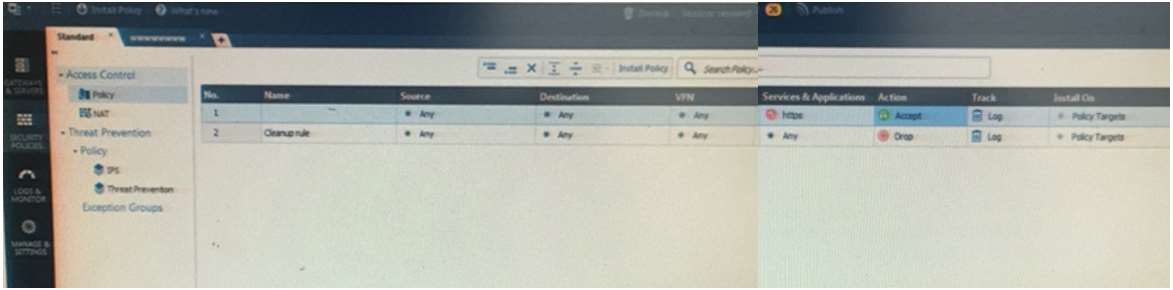
Choose the BEST describes the Policy Layer Traffic Insp…
Choose the BEST describes the Policy Layer Traffic Inspection?
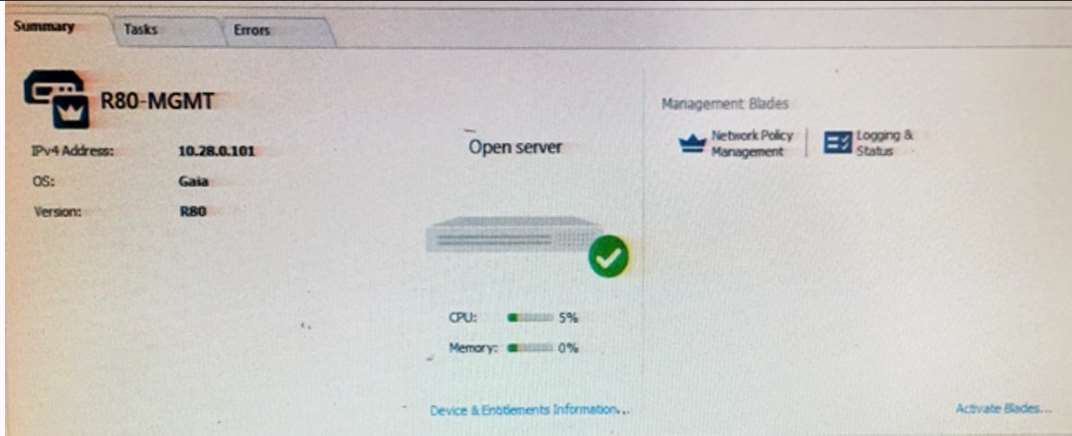
What as an ‘Open Server’?
What is a precedence of traffic inspection for the defi…
Which of the following technologies extracts detailed i…
Which of the following technologies extracts detailed information from packets and stores that information in
state tables?