Which of the following encryption algorithms is a symmetric-key encryption method that uses a 168-bit key?
Which of the following encryption algorithms is a symmetric-key encryption method that uses a
168-bit key?
Which of the following uses the same key to decrypt as it does to encrypt?
Which of the following uses the same key to decrypt as it does to encrypt?
Which method of address translation would you use?
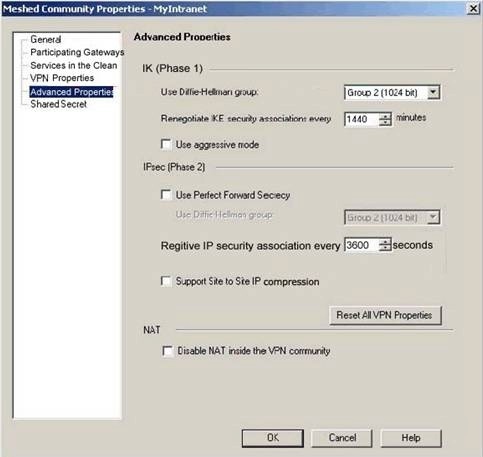
You are setting up an IKE VPN between two VPN-1/FireWall-1 Enforcement Modules protecting
two networks. One network is using an RFC 1918 compliant address range of 10.15.0.0. The other
network is using an RFC 1918 compliant address range of 192.168.9.0. Which method of address
translation would you use?
Which load-balancing mode is MOST appropriate for Dr King’s environment?
Dr Billis using VPN-1/FireWall-1 to provide load balancing for his Web servers. When a client
initiates a session with one of Dr King’s Web servers it must be able to retain its connection with
the same server for the entire session. Which load-balancing mode is MOST appropriate for Dr
King’s environment?
Which of the following explanations is MOST correct?
Which of the following conditions will cause Secure Client Verification to report that a SecureClient machine
Which of the following conditions will cause Secure Client Verification to report that a SecureClient
machine is NOT considered secured? (Choose three)
Which component of VPN-1/FireWall-1 is used for Content Security to prevent end-user access to specific URLs?
Which component of VPN-1/FireWall-1 is used for Content Security to prevent end-user access to
specific URLs?
Which of the following actions does Secure Configuration Verification perform?
Which of the following actions does Secure Configuration Verification perform? (Choose three)
Secure Configuration Verification confirms that the:
which of the following is the BEST answer?
Dr Billis his organization’s Chief Technology Officer. He is seeking a solution to control the impact
if unauthorized software on his corporate network. Dr Billhas established the following guidelines
for any solution implemented:
Required objective: The solution must not allow access to corporate resources if user’s virusprotection software is not current.Desired objective: The solution should be able to control
protocols enabled on the user’s computers.Desired objective: The solution should prevent users
snooping traffic across internal segments of the corporate network, from acquiring useful
information.
Dr King’s Security Administrator proposes SecureClient with Policy Servers, internal Enforcement
Modules, and Desktop policies as a solution. Based on the information, which of the following is
the BEST answer?
Which of the following are TRUE about SecureClient?
Which of the following are TRUE about SecureClient? (Choose three)