Which of the following statements, about Hybrid Ike, are FALSE?
Which of the following statements, about Hybrid Ike, are FALSE? Choose two.
Passwords are shared in memory instead if being written to disk, and are erased upon reboot.
Users must enter a username and a password on the first attempt while using Secure Client
Authentication window to connect to a site. Passwords are shared in memory instead if being
written to disk, and are erased upon reboot.
The IKE encryption scheme encrypts the original TCP and IP headers along with the packet data.
The IKE encryption scheme encrypts the original TCP and IP headers along with the packet data.
When licensing a VPN-1/Firewall-1 Management Server, for central licensing you must provide:
When licensing a VPN-1/Firewall-1 Management Server, for central licensing you must provide:
The type of VPN you would choose is the:
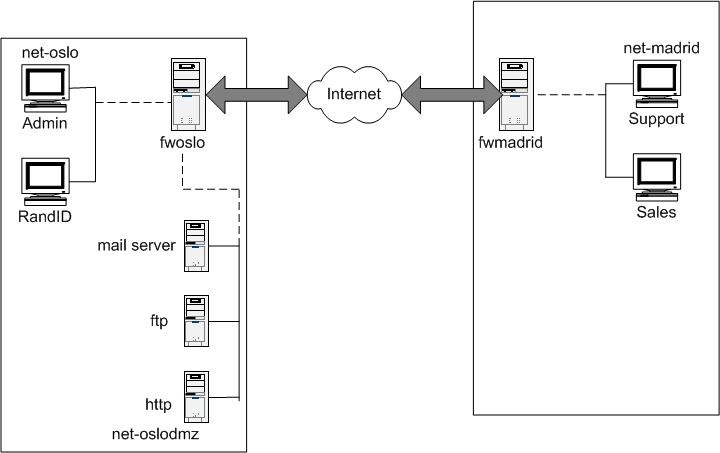
You are developing secure communications for a virtual corporation. There is a main office with a
variety of shared resources, but mist employees work either from home, or on the road. The most
common interface between these employees and the central database is a modem-equipped
Laptop. Reliability and quality are major issues for your users, and security requirements include
the need for strong authentication of the remote and mobile users. You are expected to provide
centralized management, and to anticipate significant growth in the workforce.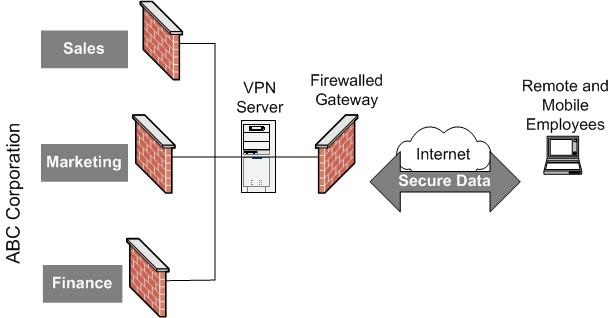
The type of VPN you would choose is the:
What method of address translation would you use?
Secure Client supports desktop policies.
Secure Client supports desktop policies.
Which encryption scheme do you choose?
You are the VPN-1/Firewall-1 administrator for a company who’s extranet requires encryption. You
must an encryption scheme with the following features:
Portability Standard
Key Management Automatic, external PKI
Session Keys Change at configured times during a connection’s life time
Which encryption scheme do you choose?
When adding users to firewall, an administrator can install just the User Database without reinstalling the en
When adding users to firewall, an administrator can install just the User Database without reinstalling the entire Security Policy.
Both, RSA and Diffie-Hellman are asymmetric encryption techniques generating a one-way trust model for encrypt
Both, RSA and Diffie-Hellman are asymmetric encryption techniques generating a one-way trust
model for encryption and decryption messages.