Which of the following statements are possible reasons …
A FortiGate 100 unit is configured to receive push updates from the FortiGuard Distribution Network,
however, updates are not being received. Which of the following statements are possible reasons
for this? (Select all that apply.)
Which of the following products can be installed on a c…
Which of the following products can be installed on a computer running Windows XP to provide
personal firewall protection, antivirus protection, web and mail filtering, spam filtering, and VPN
functionality?
which of the following types of network traffic?
DLP archiving gives the ability to store session transaction data on a FortiAnalyzer unit for which
of the following types of network traffic? (Select all that apply.)
Which of the following pieces of information can be inc…
Which of the following pieces of information can be included in the Destination Address field of a
firewall policy?
Which of the following components are contained in all …
Which of the following components are contained in all FortiGate units from the FG50 models and
up? (Select all that apply.)
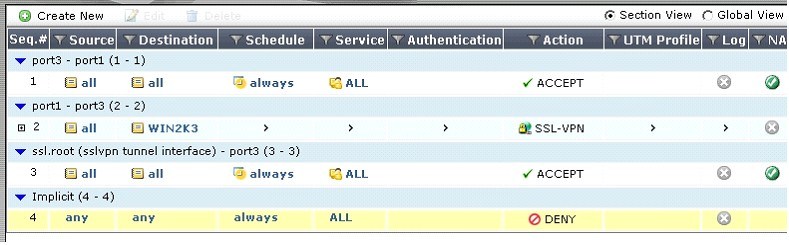
Given that the user authenticates against the SSL VP…
An end user logs into the full-access SSL VPN portal and selects the Tunnel Mode option by clicking
on the “Connect” button. The administrator has enabled split tunneling.
Given that the user authenticates against the SSL VPN policy shown in the image below, which
statement below identifies the route that is added to the client’s routing table.
Which of the following FortiAnalyzers will be detected?
An administrator configures a FortiGate unit in Transparent mode on the 192.168.11.0 subnet.
Automatic Discovery is enabled to detect any available FortiAnalyzers on the network.
Which of the following FortiAnalyzers will be detected? (Select all that apply.)
Once inside the policy, the following logic is followed:
In order to match an identity-based policy, the FortiGate unit checks the IP information. Once inside
the policy, the following logic is followed:
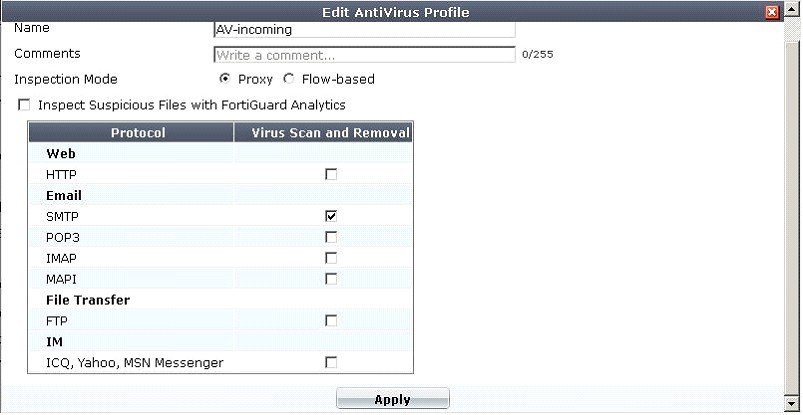
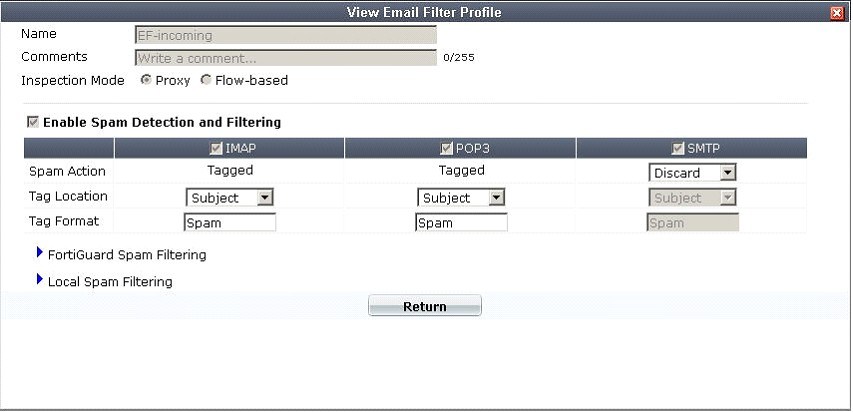
What is the correct behavior when the email attachment …
A firewall policy has been configured for the internal email server to receive email from external
parties through SMTP. Exhibits A and B show the antivirus and email filter profiles applied to this
policy.
Exhibit A:
Exhibit B:
What is the correct behavior when the email attachment is detected as a virus by the FortiGate
antivirus engine?
which of the following statements describes the action …
If no firewall policy is specified between two FortiGate interfaces and zones are not used, which of
the following statements describes the action taken on traffic flowing between these interfaces?