How does traceroute map the route a packet travels from point A to point B?
How does traceroute map the route a packet travels from point A to point B?
Which one would you suggest she looks in first?
Your lab partner is trying to find out more information about a competitors web site. The site has a
.com extension. She has decided to use some online whois tools and look in one of the regional
Internet registrys. Which one would you suggest she looks in first?
How do you defend against DHCP Starvation attack?
Which of these would be a cause for alarm?
Network Administrator Patricia is doing an audit of the network. Below are some of her findings
concerning DNS. Which of these would be a cause for alarm?
Select the best answer.
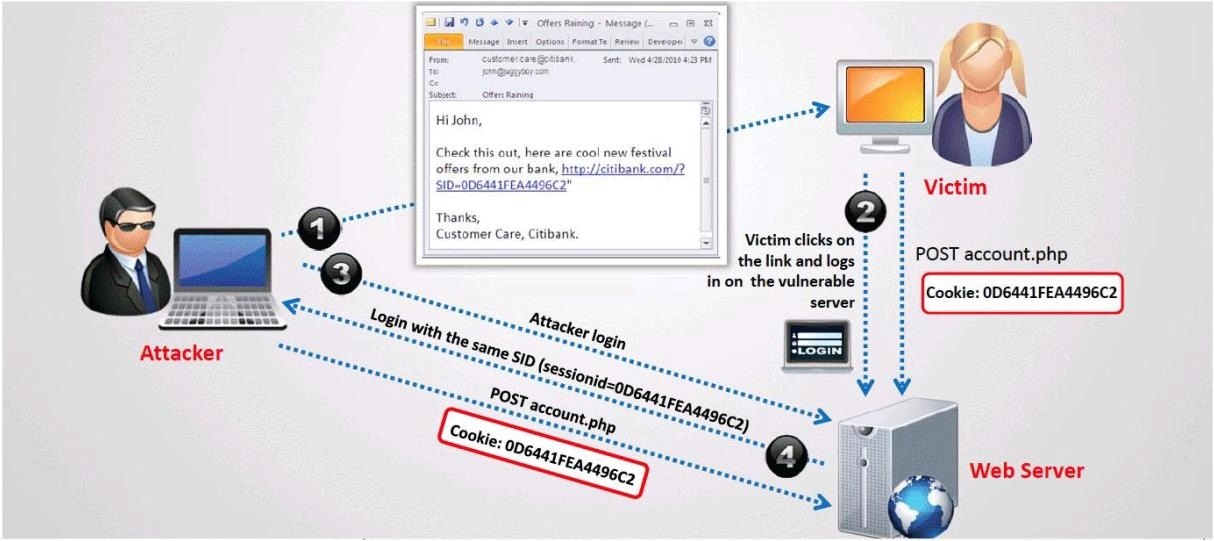
What type of session hijacking attack is shown in the exhibit?
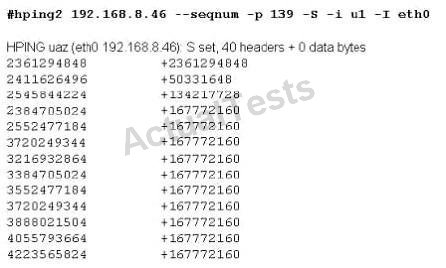
What does the first and second column mean?
How do you protect your network against SYN Flood attacks?
The SYN flood attack sends TCP connections requests faster than a machine can process them.
Attacker creates a random source address for each packet
SYN flag set in each packet is a request to open a new connection to the server from the
spoofed IP address
Victim responds to spoofed IP address,then waits for confirmation that never arrives (timeout
wait is about 3 minutes)
Victim’s connection table fills up waiting for replies and ignores new connections
Legitimate users are ignored and will not be able to access the server
How do you protect your network against SYN Flood attacks?
What is the most likely cause behind this response?
While performing a ping sweep of a subnet you receive an ICMP reply of Code 3/Type 13 for all
the pings sent out.
What is the most likely cause behind this response?
What type of port scan is shown below?
What can you infer from the above log?
The following excerpt is taken from a honeyput log. The log captures activities across three days.
There are several intrusion attempts; however, a few are successful. Study the log given below
and answer the following question:
(Note: The objective of this questions is to test whether the student has learnt about passive OS
fingerprinting (which should tell them the OS from log captures): can they tell a SQL injection
attack signature; can they infer if a user ID has been created by an attacker and whether they can
read plain source – destination entries from log entries.)
What can you infer from the above log?