What should Stephanie use so that she does not get in trouble for surfing the Internet?
Stephanie works as a records clerk in a large office building in downtown Chicago. On Monday,
she went to a mandatory security awareness class (Security5) put on by her company’s IT
department. During the class, the IT department informed all employees that everyone’s Internet
activity was thenceforth going to be monitored.
Stephanie is worried that her Internet activity might give her supervisor reason to write her up, or
worse get her fired. Stephanie’s daily work duties only consume about four hours of her time, so
she usually spends the rest of the day surfing the web. Stephanie really enjoys surfing the Internet
but definitely does not want to get fired for it.
What should Stephanie use so that she does not get in trouble for surfing the Internet?
what phase is Bob involved with?
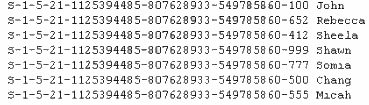
Bob has been hired to perform a penetration test on XYZ.com. He begins by looking at IP address
ranges owned by the company and details of domain name registration. He then goes to News
Groups and financial web sites to see if they are leaking any sensitive information of have any
technical details online.
Within the context of penetration testing methodology, what phase is Bob involved with?
What type of port will Neil need to setup in order to accomplish this?
Neil is a network administrator working in Istanbul. Neil wants to setup a protocol analyzer on his
network that will receive a copy of every packet that passes through the main office switch. What
type of port will Neil need to setup in order to accomplish this?
Which of the following would be the best reason for sending a single SMTP message to an address that does not
Which of the following would be the best reason for sending a single SMTP message to an
address that does not exist within the target company?
What is Jason trying to accomplish here?
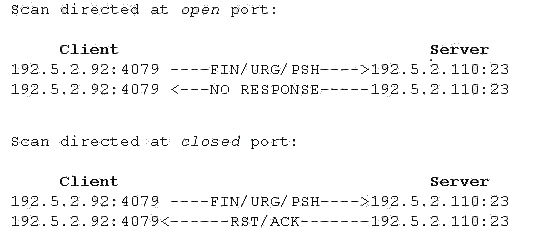
In TCP communications there are 8 flags; FIN, SYN, RST, PSH, ACK, URG, ECE, CWR. These
flags have decimal numbers assigned to them:
FIN = 1
SYN = 2
RST = 4
PSH = 8
ACK = 16
URG = 32
ECE = 64
CWR = 128
Jason is the security administrator of ASPEN Communications. He analyzes some traffic using
Wireshark and has enabled the following filters.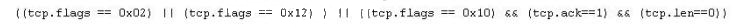
What is Jason trying to accomplish here?
What should be the next logical step that should be performed?
You are conducting a port scan on a subnet that has ICMP blocked. You have discovered 23 live
systems and after scanning each of them you notice that they all show port 21 in closed state.
What should be the next logical step that should be performed?
How can she accomplish this?
Jayden is a network administrator for her company. Jayden wants to prevent MAC spoofing on all
the Cisco switches in the network. How can she accomplish this?
Which of the following type of scans would be the most accurate and reliable option?
Ann would like to perform a reliable scan against a remote target. She is not concerned about
being stealth at this point.
Which of the following type of scans would be the most accurate and reliable option?