The signature of attack for SYN Flood contains:
SYN Flood is a DOS attack in which an attacker deliberately violates the three-way handshake
and opens a large number of half-open TCP connections. The signature of attack for SYN Flood
contains:
what should he do about the situation?
A XYZ security System Administrator is reviewing the network system log files.
He notes the following:
Network log files are at 5 MB at 12:00 noon.
At 14:00 hours,the log files at 3 MB.
What should he assume has happened and what should he do about the situation?
Which of the following type of scanning utilizes automated process of proactively identifying vulnerabilities
Which of the following type of scanning utilizes automated process of proactively identifying
vulnerabilities of the computing systems present on a network?
what concept in the realm of email security?
To what does “message repudiation” refer to what concept in the realm of email security?
How will you delete the OrdersTable from the database using SQL Injection?
The following script shows a simple SQL injection. The script builds an SQL query by
concatenating hard-coded strings together with a string entered by the user: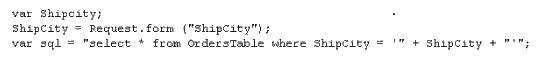
The user is prompted to enter the name of a city on a Web form. If she enters Chicago, the query
assembled by the script looks similar to the following:
SELECT * FROM OrdersTable WHERE ShipCity = ‘Chicago’
How will you delete the OrdersTable from the database using SQL Injection?
What is odd about this attack?
Snort has been used to capture packets on the network. On studying the packets, the penetration
tester finds it to be abnormal. If you were the penetration tester, why would you find this
abnormal?
What is odd about this attack? (Choose the most appropriate statement)
What are the limitations of Vulnerability scanners?
What are the limitations of Vulnerability scanners? (Select 2 answers)
which are the four existing Regional Internet Registry (RIR’s)?
Your XYZ trainee Sandra asks you which are the four existing Regional Internet Registry (RIR’s)?
Where can Stephanie go to see past versions and pages of a website?
Stephanie works as senior security analyst for a manufacturing company in Detroit. Stephanie
manages network security throughout the organization. Her colleague Jason told her in confidence
that he was able to see confidential corporate information posted on the external website
http://www.jeansclothesman.com. He tries random URLs on the company’s website and finds
confidential information leaked over the web. Jason says this happened about a month ago.
Stephanie visits the said URLs, but she finds nothing. She is very concerned about this, since
someone should be held accountable if there was sensitive information posted on the website.
Where can Stephanie go to see past versions and pages of a website?
A very useful resource for passively gathering information about a target company is:
A very useful resource for passively gathering information about a target company is:

