HOTSPOT
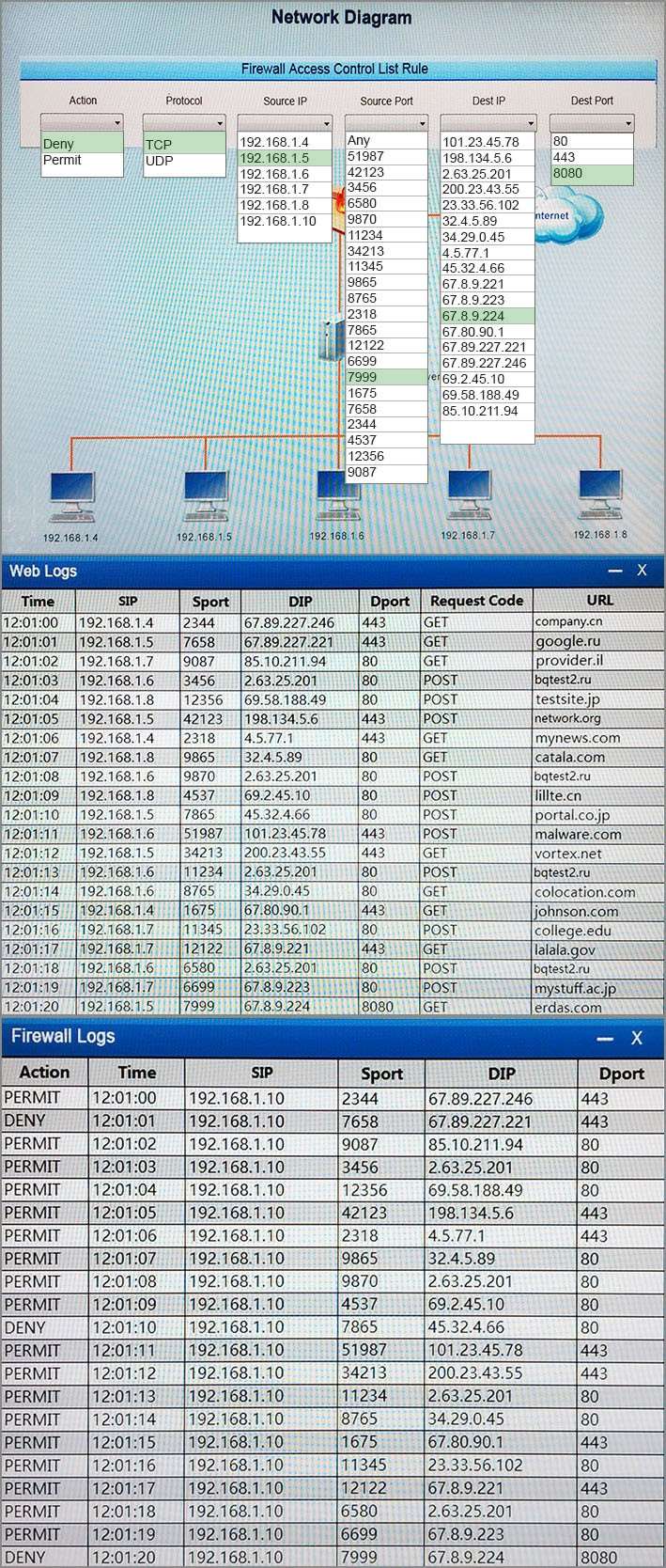
A security analyst suspects that a workstation may be beaconing to a command and control server. You must inspect the logs from the company’s web proxy server and the firewall to determine the best course of action to take in order to neutralize the threat with minimum impact to the organization.
Instructions:
If at any time you would like to bring back the initial state of the simulation, please select the Reset button.
When you have completed the simulation, please select the Done button to submit. Once the simulation is submitted, please select the Next button to continue.
Hot Area: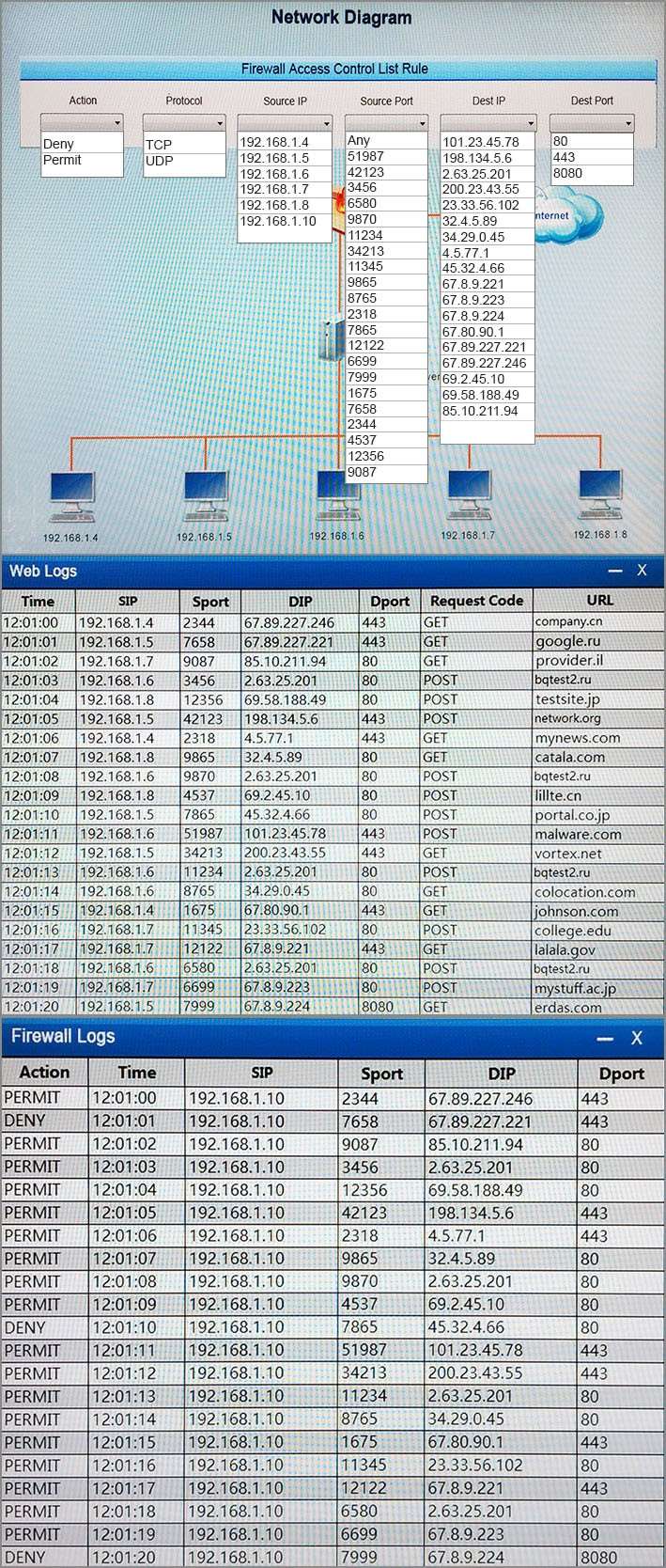

Answer: See the explanation.