A cybersecurity analyst has received the laptop of a user who recently left the company. The analyst types
‘history’ into the prompt, and sees this line of code in the latest bash history: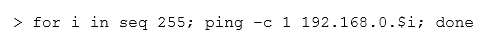
This concerns the analyst because this subnet should not be known to users within the company. Which of the following describes what this code has done on the network?

A.
Performed a ping sweep of the Class C network.
B.
Performed a half open SYB scan on the network.
C.
Sent 255 ping packets to each host on the network.
D.
Sequentially sent an ICMP echo reply to the Class C network.
Explanation:

