Which of the following threat actors is MOST likely to …
Which of the following threat actors is MOST likely to steal a company’s proprietary information to gain a
market edge and reduce time to market?
Which of the following should the analyst implement to …
A security analyst is hardening a server with the directory services role installed. The analyst must ensure LDAP traffic cannot be monitored or sniffed and maintains compatibility with LDAP clients.
Which of the following should the analyst implement to meet these requirements? (Select two.)
Which of the following attacks specifically impact data…
Which of the following attacks specifically impact data availability?
Which of the following certificate formats should the e…
A security engineer is configuring a system that requires the X.509 certificate information to be pasted into a
form field in Base64 encoded format to import it into the system. Which of the following certificate formats
should the engineer use to obtain the information in the required format?
what the CIO has requested?
In a corporation where compute utilization spikes several times a year, the Chief Information Officer (CIO) has
requested a cost-effective architecture to handle the variable capacity demand. Which of the following
characteristics BEST describes what the CIO has requested?
Which of the following BEST describes an important secu…
Which of the following BEST describes an important security advantage yielded by implementing vendor
diversity?
Which of the following should be implemented if all the…
Multiple organizations operating in the same vertical wants to provide seamless wireless access for their
employees as they visit the other organizations. Which of the following should be implemented if all the
organizations use the native 802.1x client on their mobile devices?
Which of the following should the security analyst do t…
A security analyst is diagnosing an incident in which a system was compromised from an external IP address.
The socket identified on the firewall was traced to 207.46.130.0:6666. Which of the following should the security
analyst do to determine if the compromised system still has an active connection?
Drag and drop the appropriate security controls on the floor plan.
DRAG DROP
You have been tasked with designing a security plan for your company. Drag and drop the appropriate security controls on the floor plan.
Instructions: All objects must be used and all place holders must be filled. Order does not matter. When you have completed the simulation, please select the Done button to submit.
Select and Place: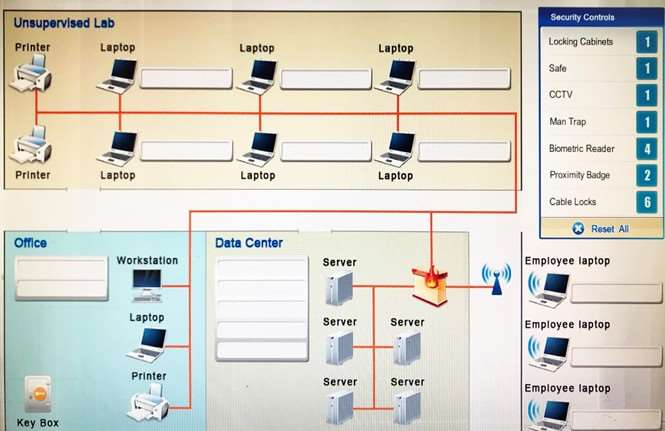
Which of the following would a security specialist be a…
Which of the following would a security specialist be able to determine upon examination of a server’s
certificate?

