Which of the following describes a typical commercial software license?
You have two computers, each with a different operating system. One is a Linux system, which
uses the Gnu Public License (GPL). You can use this Linux software free of charge, and you can
make changes to code that created the operating system. The other system is a Windows system.
Which of the following describes a typical commercial software license?
Which client application could benefit from the use of a callback object?
Which client application could benefit from the use of a callback object?
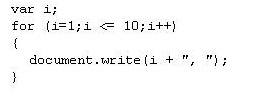
What kind of code is shown in the preceding example?
Consider the following code:
<film>
<year>1942</year>
<title>Casablanca</title>
<director>Michael Curtiz</director>
</film>
What kind of code is shown in the preceding example?
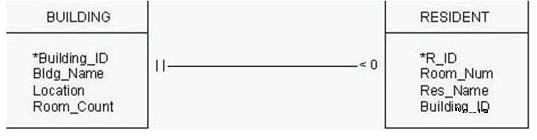
What is the relationship between BUILDING and RESIDENT?
What is the single most important result of any marketing strategy?
What is the single most important result of any marketing strategy?
What output will appear in the browser when you run this script?
which type of encryption when it sends a SetRequest command?
Simple network management protocol (SNMP) uses which type of encryption when it sends a
SetRequest command?
Which e-commerce protocol is defined as the interorganization exchange of documents in standardized electronic
Which e-commerce protocol is defined as the interorganization exchange of documents in
standardized electronic form directly between participating computers?
What should Jim configure his mail server?
Jim is configuring his new mail server but he can’t remember the well-known port for
SMTP. What should Jim configure his mail server?
Which of the following can you implement on the firewall to alleviate this problem?
Company employees have noticed that the quality of voice calls on their Cisco IP phones is greatly
reduced at various times during the day. After investigating the problem, you notice that the times
when voice quality is reduced coincides with heavy e-mail traffic. Which of the following can you
implement on the firewall to alleviate this problem?