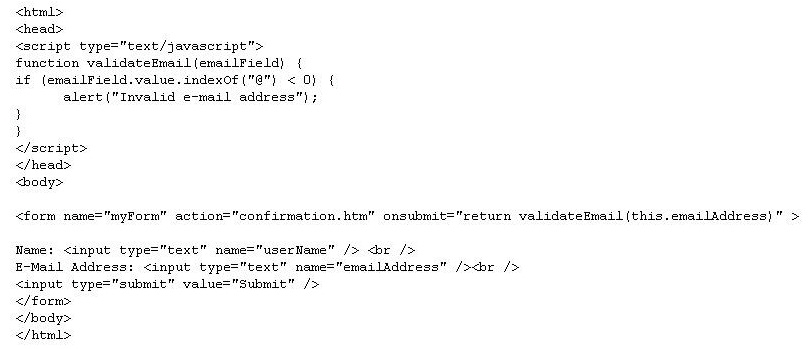
What changes need to be made to the script in order to abort the submission if an invalid e-mail address is en
which of the following ensures that messages end on a 64-bit boundary?
Within the Encrypted Security Payload (ESP) extension header, which of the following ensures
that messages end on a 64-bit boundary?
Which of the following Web site maintenance functions helps ensure that users continue to visit your site?
Which of the following Web site maintenance functions helps ensure that users continue to visit
your site?
Which of the following services is an example of a Mail Transfer Agent (MTA)?
Which of the following services is an example of a Mail Transfer Agent (MTA)?
Which of the following must you do to create a cheroot jail?
Which of the following must you do to create a cheroot jail?
Which of the following lists the appropriate parties to inform?
A security breach has occurred involving the company e-commerce server. Customer credit card
data has been released to unauthorized third parties. Which of the following lists the appropriate
parties to inform?
Classes should be grouped into packages by:
Classes should be grouped into packages by:
what two techniques should be used to release an attribute called Cart stored in an HttpSession?
In the J2EE 1.3, what two techniques should be used to release an attribute called Cart stored in
an HttpSession?
Which of the following are the valid methods for handling SQL exceptions generated in JDBC (Choose all that ap
Which of the following are the valid methods for handling SQL exceptions
generated in JDBC (Choose all that apply.?
Which service, command or tool allows a remote user to interface with a system as if he were sitting at the te
Which service, command or tool allows a remote user to interface with a system as if he were
sitting at the terminal?