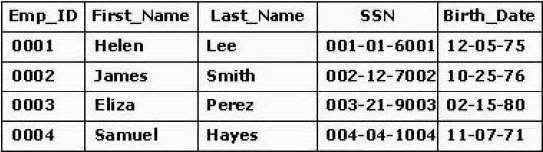
What is the degree of the table?
Which type of encryption is typically slower to use but does not require a secure channel to function?
Which type of encryption is typically slower to use but does not require a secure channel to
function?
What is the expected result when you run this script in the browser?
Why was the IPv6 Time To Live (TTL) field changed to the Hop Limit field in IPv6?
Why was the IPv6 Time To Live (TTL) field changed to the Hop Limit field in IPv6?
Which of the following is the most efficient method for documenting and communicating a Web site plan?
Which of the following is the most efficient method for documenting and communicating a Web site
plan?
Which command should Nadir enter to ensure that his Perl script will execute securely?
Nadir installed a Perl script in the cgi-bin directory of his Linux system that is running
apache server. NO significant modifications have been made to Apache server. He
accesses a script named test.cgi via a web browser, but the script does not execute, and
Apache server returns a 500 “Internal Server Error” message. Nadir executes the
command is-al on the cgi-bin directory of the problem server. He learns that the
permissions on test.cgi are 700, and that the file is owned by root. Which command
should Nadir enter to ensure that his Perl script will execute securely?
which resources to protect?
You want to prioritize resources due to limited funds. Which of the following strategies is best to
help you determine which resources to protect?
which layer of the OSI/RM?
The most popular types of proxy-oriented firewalls operate at which layer of the OSI/RM?
what layers should the model be aware of?
In a well-designed application that implements to Model-View-Persistence layering, what layers
should the model be aware of?
Which of the following methods should be used by a client to obtain a JNDI initial context and create the most
Which of the following methods should be used by a client to obtain a JNDI initial context and
create the most portable code?