Which of the following provides the greatest potential to allow someone to avoid the firewall and attack the i
Which of the following provides the greatest potential to allow someone to avoid the firewall and
attack the internal network?
what can be done to solve the problem?
A CGI application on the company’s Web server has a bug written into it. This particular bug
allows the application to write data into an area of memory that has not been properly allocated to
the application. An attacker has created an application that takes advantage of this bug to obtain
credit card information. Which of the following security threats is the attacker exploiting, and what
can be done to solve the problem?
Which one of the following OOAD artifacts would be MOST useful in helping to plan the content of iterations in
Which one of the following OOAD artifacts would be MOST useful in helping to plan the content of
iterations in a project plan?
Which of the following CANNOT be passed in a JAX-RPC remote method invocation?
Which of the following CANNOT be passed in a JAX-RPC remote method invocation?
which of the following methods?
Under JDBC, you can move the cursor within the resultset to a particular specified
row using which of the following methods?
which type of enterprise bean does this process refer?
An EJB client invokes a create() method. An EJB container instantiates an enterprise bean as the
result of this method call. The bean is then held in a pool awaiting a method invocation. To which
type of enterprise bean does this process refer?
Which of these technologies is most likely to cause customers problems with their browsers when they try to ac
You are working for a financial services company. The company has a Web site that allows its
customers to review their statements online. Your Web site uses the Document Object Model
(DOM), ActiveX, JavaScript and Java. Which of these technologies is most likely to cause
customers problems with their browsers when they try to access information?
What log should you check?
You are logged on to a Windows system. You suspect a problem with your Oracle database, and
want to view the pertinent information related to the problem. What log should you check?
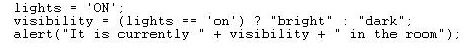
What will this alert display?
What is the address prefix in binary for multicast addresses?
What is the address prefix in binary for multicast addresses?