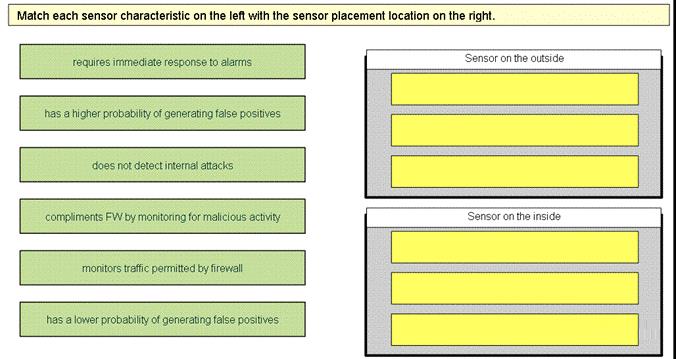
Match each sensor characteristic on the left with the sensor placement location on the right.
What is the best way to mitigate the risk that executable-code exploits will perform malicious acts such as er
What is the best way to mitigate the risk that executable-code exploits will perform malicious acts
such as erasing your hard drive?
Which type of signature engine is best suited for creating custom signatures that inspect data at Layer 5 and
Which type of signature engine is best suited for creating custom signatures that inspect data at
Layer 5 and above?
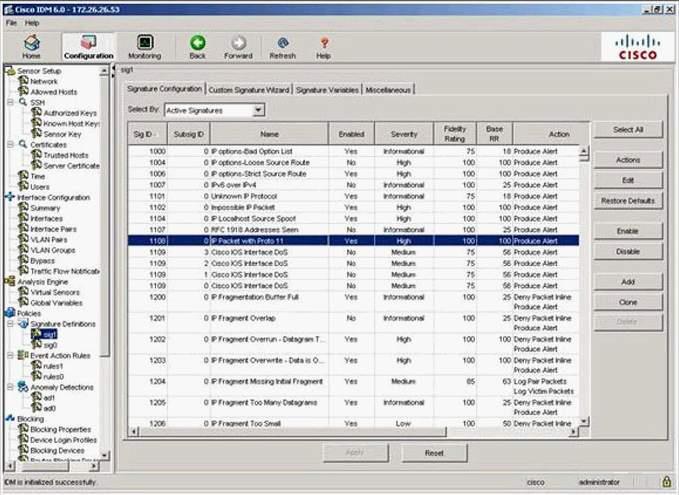
Which of the following should you select to view and change the required parameters?
What should you do next?
You would like to investigate an incident and have already enabled the Log Pair Packets action on
various signatures being triggered. What should you do next?
Which signature action or actions should be selected to cause the attacker’s traffic flow to terminate w
Which signature action or actions should be selected to cause the attacker’s traffic flow to
terminate when the Cisco IPS Sensor is operating in promiscuous mode?
What precaution must you keep in mind when adding, editing, or deleting allowed hosts on a Cisco IPS Sensor?
You are using Cisco IDM. What precaution must you keep in mind when adding, editing, or
deleting allowed hosts on a Cisco IPS Sensor?
Which action does the copy /erase ftp://172.26.26.1/sensor_config01 current-config command perform?
Which action does the copy /erase ftp://172.26.26.1/sensor_config01 current-config command
perform?
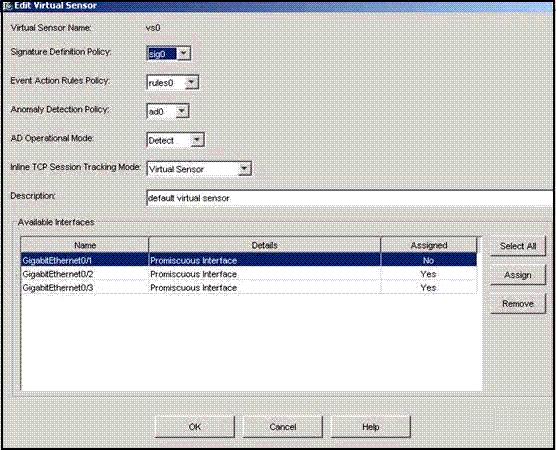
Which interfaces are assigned to an inline VLAN pair?
Which character must precede a variable to indicate that you are using a variable rather than a string?
Which character must precede a variable to indicate that you are using a variable rather than a
string?