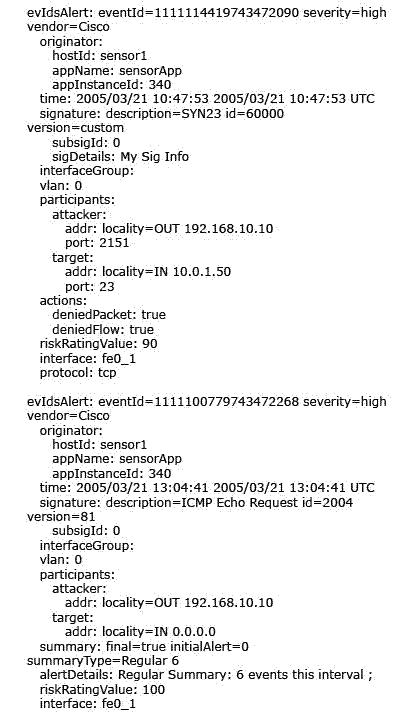
What is an appropriate action to take?
How does a Cisco network sensor detect malicious network activity?
How does a Cisco network sensor detect malicious network activity?
Which three steps must you perform to prepare sensor interfaces for inline operations?
Which three steps must you perform to prepare sensor interfaces for inline operations? (Choose
three.)
Which two should you use to accomplish your goal in the most time-efficient manner?
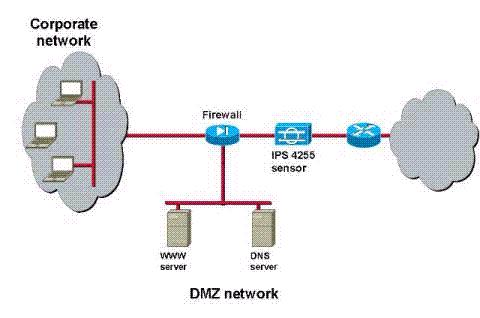
Refer to the exhibit. You are the security administrator for the network in the exhibit. You want
your inline Cisco IPS 4255 sensor to drop packets that pose the most severe risk to your network,
especially to the servers on your DMZ.
Which two should you use to accomplish your goal in the most time-efficient manner? (Choose
two.)
Which command resets all signature settings back to the factory defaults?
Which command resets all signature settings back to the factory defaults?
which purpose is a sensor license needed?
For which purpose is a sensor license needed?
Which two are not forwarded to the NM-CIDS?
Which two are not forwarded to the NM-CIDS? (Choose two.)
(Choose three.)
Your network has only one entry point. However, you are concerned about internal attacks. Select
the three best choices for your network. (Choose three.)
which scenario are an AIC engine and the Application Policy Enforcement feature needed?
In which scenario are an AIC engine and the Application Policy Enforcement feature needed?
What is the primary function of a Master Blocking Sensor?
What is the primary function of a Master Blocking Sensor?