Which Cisco IOS command is used to verify that either the Cisco IOS image, the configuration files, or both ha
Which Cisco IOS command is used to verify that either the Cisco IOS image, the configuration files, or both have been properly backed up and secured?
What does the secure boot-config global configuration accomplish?
What does the secure boot-config global configuration accomplish?
When using a stateful firewall, which information is stored in the stateful session flow table?
When using a stateful firewall, which information is stored in the stateful session flow table?
Which statement is true about configuring access control lists to control Telnet traffic destined to the route
Which statement is true about configuring access control lists to control Telnet traffic destined to the router itself?
When configuring role-based CLI on a Cisco router, which step is performed first?
When configuring role-based CLI on a Cisco router, which step is performed first?
Which characteristic is a potential security weakness of a traditional stateful firewall?
Which characteristic is a potential security weakness of a traditional stateful firewall?
Which statement is true?
What will be disabled as a result of the no service password-recovery command?
What will be disabled as a result of the no service password-recovery command?
What does the MD5 algorithm do?
What does the MD5 algorithm do?
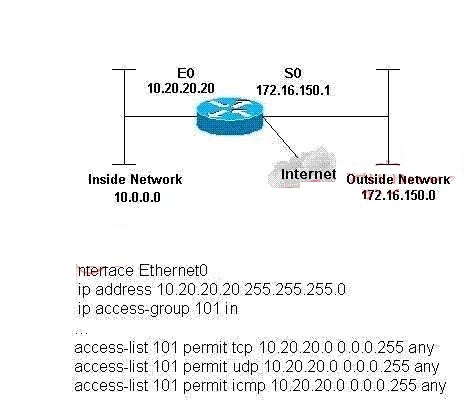
What happens when traffic being filtered by the access list does not match the configured ACL statements for S
You have configured a standard access control list on a router and applied it to interface Serial 0 in an outbound direction. No ACL is applied to Interface Serial 1 on the same router. What happens when traffic being filtered by the access list does not match the configured ACL statements for Serial 0?