Which step is important to take when implementing secure network management?
Which step is important to take when implementing secure network management?
Which statement best represents the characteristics of a VLAN?
Which statement best represents the characteristics of a VLAN?
Which Layer 2 protocol provides loop resolution by managing the physical paths to given network segments?
Which Layer 2 protocol provides loop resolution by managing the physical paths to given network segments?
Which statement is true when you have generated RSA keys on your Cisco router to prepare for secure device man
Which statement is true when you have generated RSA keys on your Cisco router to prepare for secure device management?
What is the key difference between host-based and network-based intrusion prevention?
What is the key difference between host-based and network-based intrusion prevention?
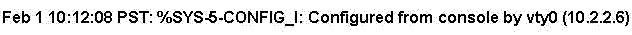
Based on the Syslog message shown, which two statements are true? (Choose two.)
Which four methods are used by hackers? (Choose four.)
Which four methods are used by hackers? (Choose four.)
Which statement about Cisco IOS IPS on Cisco IOS Release 12.4(11)T and later is true?
Which statement about Cisco IOS IPS on Cisco IOS Release 12.4(11)T and later is true?
Which characteristic is the foundation of Cisco Self-Defending Network technology?
Which characteristic is the foundation of Cisco Self-Defending Network technology?
Which kind of table do most firewalls use today to keep track of the connections through the firewall?
Which kind of table do most firewalls use today to keep track of the connections through the firewall?