Two of the switches are deployed as core switches
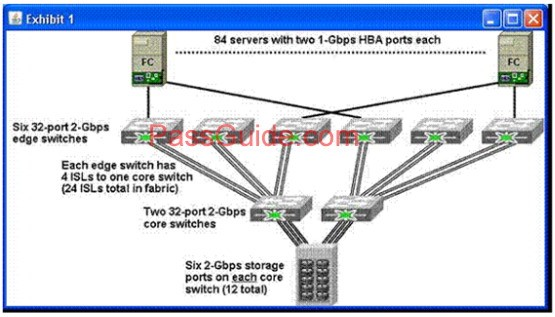
Refer to the exhibit.
Build Your Dreams
You are designing a new SAN the existing SAN uses eight 32-port 2-Gbps Fibre Channel switches. Two of the switches are deployed as core switches, and the remaining six switches are deployed as edge switches. Each edge switch has four ISLs to one of the two core switches. The disk array has twelve 2-Gbps Fibre Channel ports. Each of the 84 servers has a dual-port 1-Gbps Fibre Channel HBA.
which power mode does the switch operate?
Your Cisco MDS 9509 configuration requires 2000 watts of power and is configured with two 2500W power supplies if 110V power is provided to the switch, in which power mode does the switch operate?
Which option will allow this testto occur?
A SAN administrator would like to test FCIP using the existing 18/4-Port Multiservice Module in a Cisco MDS 9500 switch that is currently used for iSCSI connectivity. To test FCIP, the administrator should use the SAN extension over IP package. Which option will allow this test
Build Your Dreams
to occur?
which power mode does the switch operate?
Your Cisco MDS 9509 configuration requires 2000 watts of power and is configured with two 2500W power supplies if 110V power is provided to the switch, in which power mode does the switch operate?
To protect the supervisor of a Cisco Nexus 7000 switch, the CoPP feature performs which two functions? (Choose
To protect the supervisor of a Cisco Nexus 7000 switch, the CoPP feature performs which two functions? (Choose two.)
What are three benefits of storage consolidation? (Choose three
What are three benefits of storage consolidation? (Choose three.)
Which design should you avoid?
Your customer plans to deploy FWSM and IDSM modules in the aggregation layer. Which design should you avoid?
What should be implemented to mitigate man-in-middle attacks in the data access layer?
What should be implemented to mitigate man-in-middle attacks in the data access layer?
Which condition requires a Layer 2 access design?
Which condition requires a Layer 2 access design?
Which two kinds of applications require sustained throughput and are sensitive to latency? (Choose two
Which two kinds of applications require sustained throughput and are sensitive to latency? (Choose two.)