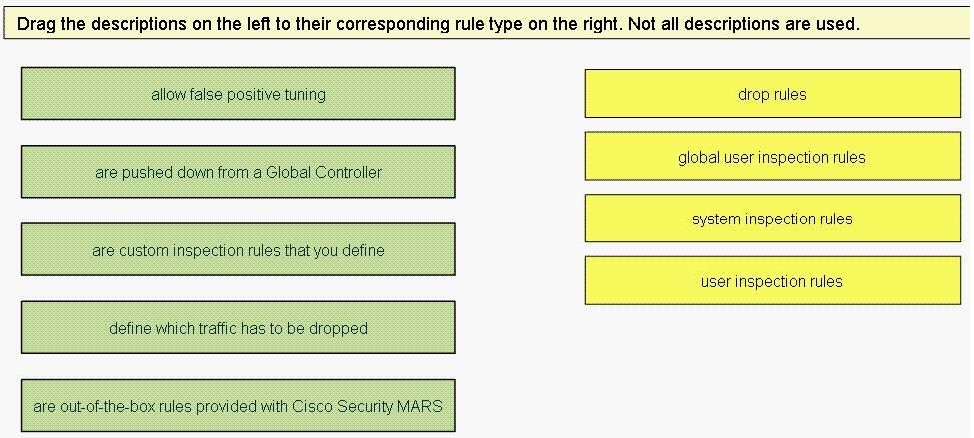
Identify two ways to create a long-duration query on the Cisco Security MARS appliance. (Choose two.)
Identify two ways to create a long-duration query on the Cisco Security MARS appliance. (Choose two.)
Which two of these statements describe features of the NAC Appliance architecture. (Choose two.)
Which two of these statements describe features of the NAC Appliance architecture. (Choose two.)
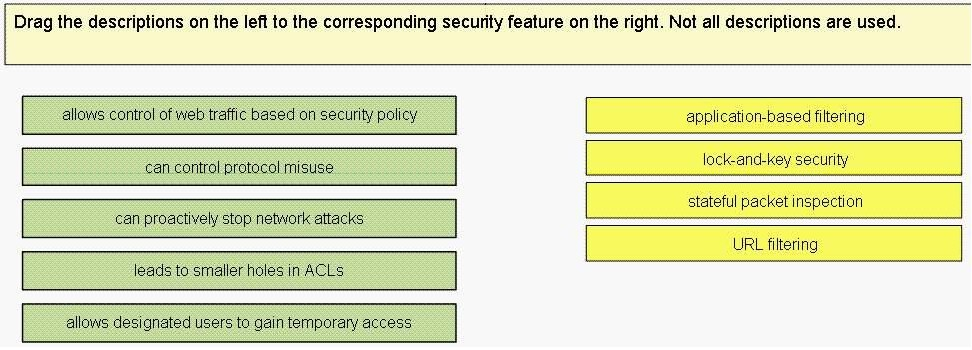
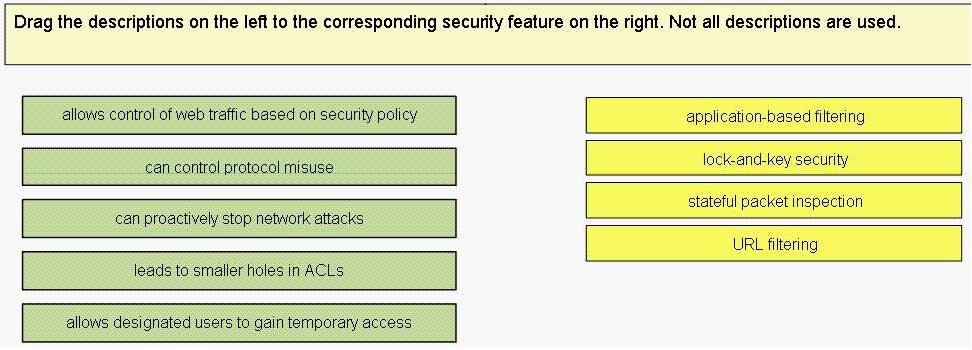
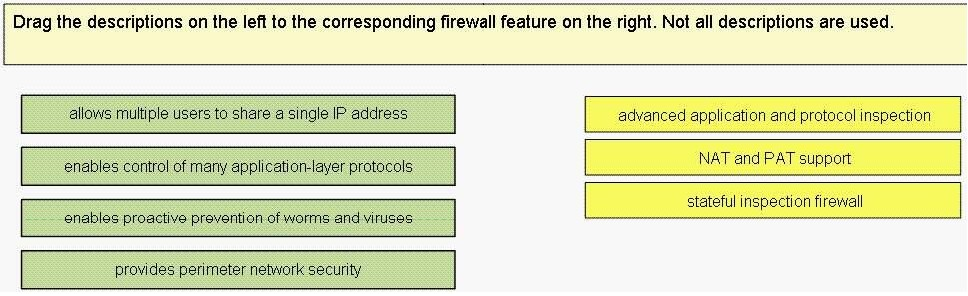
Drag the descriptions on the left to the corresponding security feature on the right?
Drag the descriptions on the left to the corresponding security feature on the right?
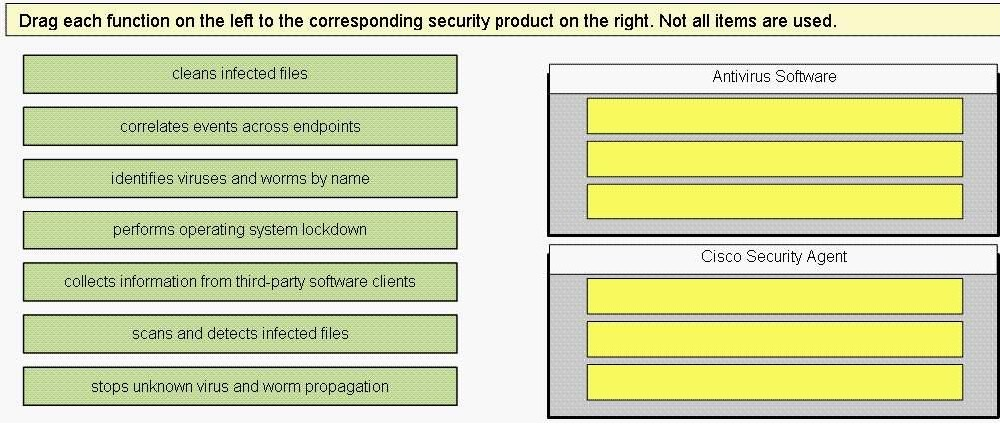
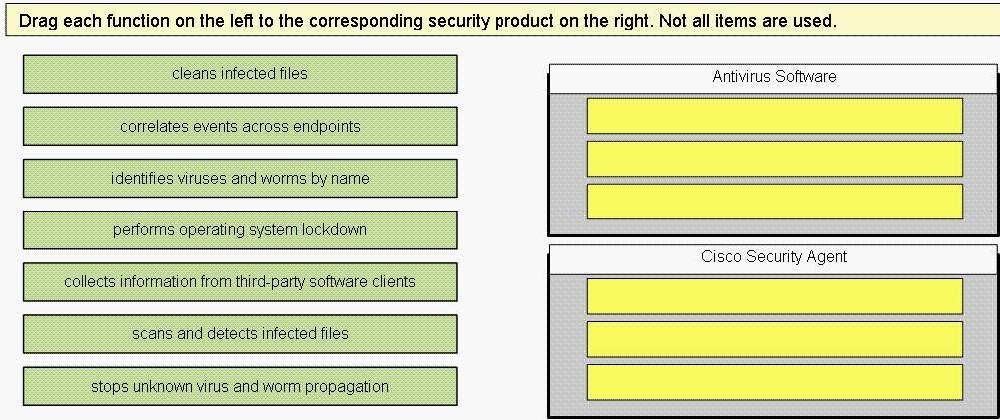
Drag each function on the left to the corresponding cesurity product on the right?
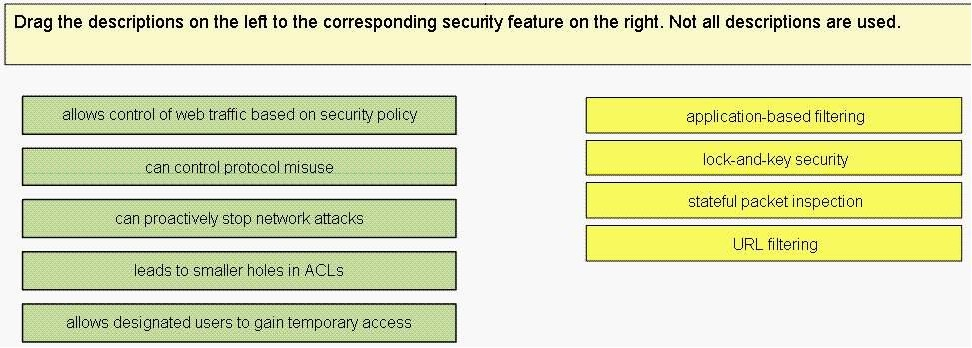
Drag the descriptions on the left to the corresponding security feature on the right?
Identify three components of the anti-X defense pillar. (Choose three.)
SomeCompany, Ltd. wishes to adopt the Adaptive Threat Defense architecture in their security policy. Identify three components of the anti-X defense pillar. (Choose three.)