What is the correct command structure, once entering the route command, to implement ospf successfully?
You need to publish SecurePlatform routes using the ospf routing protocol. What is the correct
command structure, once entering the route command, to implement ospf successfully?
How are these connections secured?
Control connections between the Security Management Server and the Gateway are not
encrypted by the VPN Community. How are these connections secured?
How does a cluster member take over the VIP after a failover event?
How does a cluster member take over the VIP after a failover event?
Which command line tool can you use?
You want to verify that your Check Point cluster is working correctly. Which command line tool can
you use?
it is the basis for Check Point ClusterXL intermodule communication.
________is a proprietary Check Point protocol. it is the basis for Check Point ClusterXL intermodule communication.
What’s happening?
Which of the following commands is the best for testing the connectivity of the crossover cable?
You are MegaCorp Security Administrator. This company uses a firewall cluster, consisting of two
cluster members. The cluster generally works well but one day you find that the cluster is behaving
strangely. You assume that there is a connectivity problem with the cluster synchronization cluster
link (cross-over cable).
Which of the following commands is the best for testing the connectivity of the crossover cable?
What are the restrictions of this solution?
Organizations are sometimes faced with the need to locate cluster members in different
geographic locations that are distant from each other. A typical example is replicated data centers
whose location is widely separated for disaster recovery purposes.
What are the restrictions of this solution?
What is the problem with this configuration?
You are establishing a ClusterXL environment, with the following topology: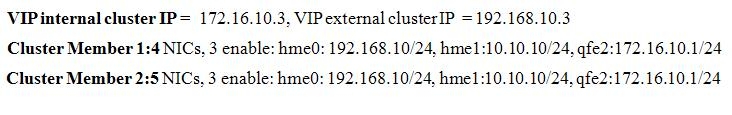
External interfaces 192.168.10.1 and 192.168.10.2 connect to a VLAN switch. The upstream
router connects to the same VLAN switch. Internal interfaces 172.16 10.1 and 172.16.10.2
connect to a hub. 10.10.10.0 is the synchronization network. The Security Management Server is
located on the internal network with IP 172.16.10.3. What is the problem with this configuration?