What is this technique called?
This IDS defeating technique works by splitting a datagram (or packet) into multiple fragments and
the IDS will not spot the true nature of the fully assembled datagram. The datagram is not
reassembled until it reaches its final destination. It would be a processor-intensive task for IDS to
reassemble all fragments itself, and on a busy system the packet will slip through the IDS onto the
network. What is this technique called?
What two things will happen if a router receives an ICMP packet, which has a TTL value of 1, and the destinati
What two things will happen if a router receives an ICMP packet, which has a TTL value of 1, and
the destination host is several hops away? (Select 2 answers)
How would you prevent such type of attacks?
Which of the following LM hashes represents a password of less than 8 characters?
Which of the following LM hashes represents a password of less than 8 characters?
This type of Port Scanning technique splits TCP header into several packets so that the packet filters are not
This type of Port Scanning technique splits TCP header into several packets so that the packet
filters are not able to detect what the packets intends to do.
What can he infer from this file?
How would you call this type of activity?
Joel and her team have been going through tons of garbage, recycled paper, and other rubbish in
order to find some information about the target they are attempting to penetrate. How would you
call this type of activity?
What technique could Harold use to sniff his agency’s switched network?
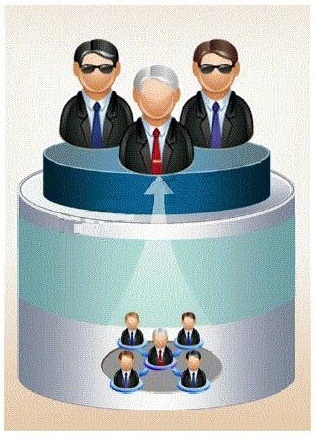
Harold is the senior security analyst for a small state agency in New York. He has no other
security professionals that work under him, so he has to do all the security-related tasks for the
agency. Coming from a computer hardware background, Harold does not have a lot of experience
with security methodologies and technologies, but he was the only one who applied for the
position. Harold is currently trying to run a Sniffer on the agency’s network to get an idea of what
kind of traffic is being passed around, but the program he is using does not seem to be capturing
anything. He pours through the Sniffer’s manual, but cannot find anything that directly relates to
his problem. Harold decides to ask the network administrator if he has any thoughts on the
problem. Harold is told that the Sniffer was not working because the agency’s network is a
switched network, which cannot be sniffed by some programs without some tweaking. What
technique could Harold use to sniff his agency’s switched network?
which situations would you want to use anonymizer?
Anonymizer sites access the Internet on your behalf, protecting your personal information from
disclosure. An anonymizer protects all of your computer’s identifying information while it surfs for
you, enabling you to remain at least one step removed from the sites you visit.
You can visit Web sites without allowing anyone to gather information on sites visited by you.
Services that provide anonymity disable pop-up windows and cookies, and conceal visitor’s IP
address.
These services typically use a proxy server to process each HTTP request. When the user
requests a Web page by clicking a hyperlink or typing a URL into their browser, the service
retrieves and displays the information using its own server. The remote server (where the
requested Web page resides) receives information on the anonymous Web surfing service in
place of your information.
In which situations would you want to use anonymizer? (Select 3 answers)
Which Windows system tool checks integrity of critical files that has been digitally signed by Microsoft?
Which Windows system tool checks integrity of critical files that has been digitally signed by
Microsoft?