What access list for Router B would accomplish this?
Click the Exhibit button to view the configuration.
The network associated with Router A’s Ethernet 0 port is designed to be publicly accessible. However, Router B’s Token Ring 0 network should be accessible only to hosts from Router A’s Ethernet 0 network.
What access list for Router B would accomplish this?
What are the three primary CTM product modules?
What are the three primary CTM product modules?
Which two operational states can PVCs be in?
Which two operational states can PVCs be in? (multiple answer)
What is NOT a key differentiator that Cisco offers to customers with the MDS that our competitors cannot?
What is NOT a key differentiator that Cisco offers to customers with the MDS that our competitors cannot?
The spectral characteristic in the 1558nm to 1559nm range is commonly known as
What is the approximate spacing between channels?
What Frame Relay Traffic Shaping map-class sub-command should be entered on Router A to prevent workstation A
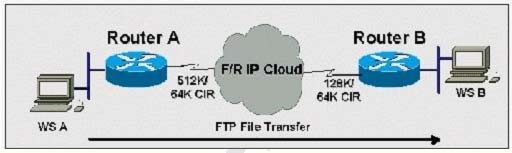
Click the Exhibit to view the topology.
Router A has a 512K-access port into the frame relay cloud. Router B has 128K-access port into the frame relay cloud. The two routers are connected with symmetrical PVCs that are configured for 64K committed information rate (CIR). What Frame Relay Traffic Shaping map-class sub-command should be entered on Router A to prevent workstation A from overrunning the access port on Router B?
Following diagram put the events listed below in correct chronological sequence.
Click the Exhibit button.
If you have a fiber cut on all four fibers between nodes C and D in the following diagram put the events listed below in correct chronological sequence.
1. node A loops back traffic in the direction of node E
2. node D initiates a line switch and signals the fact in the K2 byte
3. node C loops back traffic in the direction of node B
4. both sides switch traffic to the protect channel and the circuit is restored in less than 50 ms
5. nodes C detects the loss of signal and signals the fact in the K1 byte