Which two statements about these attacks are true?
The Company security administrator is concerned with layer 2 network attacks. Which two
statements about these attacks are true? (Select two)
Which statement is true about DHCP spoofing operation?
The Company security administrator wants to prevent DHCP spoofing. Which statement is
true about DHCP spoofing operation?
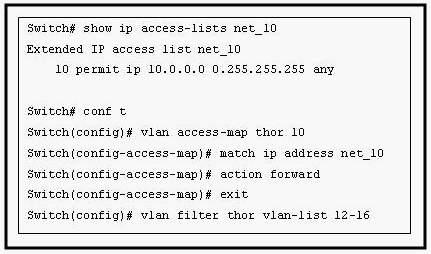
What will happen to traffic within VLAN 14 with a source address of 172.16.10.5?
which three protocols are allowed through the switch port before authentication takes place?
Company is implementing 802.1X in order to increase network security. In the use of 802.1X
access control, which three protocols are allowed through the switch port before
authentication takes place? (Select three)
What configuration will isolate the servers from each other?
Refer to the exhibit. The web servers WS_1 and WS_2 need to be accessed by external and
internal users. For security reasons, the servers should not communicate with each other,
although they are located on the same subnet. The servers do need, however, to
communicate with a database server located in the inside network. What configuration will
isolate the servers from each other?
Which of the following actions are taken in a VLAN map that does not contain a match clause?
VLAN maps have been configured on switch R1. Which of the following actions are taken in
a VLAN map that does not contain a match clause?
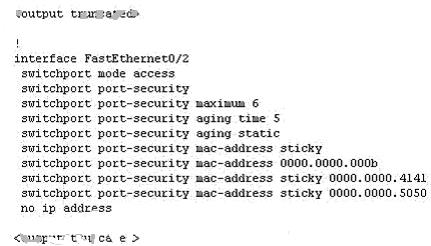
what happens when a host with the MAC address of 0003.0003.0003 is directly connected to the switch port?
A Company switch was configured as shown below:
switchport mode access
switchport port-security
switchport port-security maximum 2
switchport port-security mac-address 0002.0002.0002
switchport port-security violation shutdown
Given the configuration output shown above, what happens when a host with the MAC
address of 0003.0003.0003 is directly connected to the switch port?
Which interface or interfaces on switch SW_A can have the port security feature enabled?
what two conclusions can be deduced?
Which two statements are true about this technology?
You need to configure port security on switch R1. Which two statements are true about this
technology? (Select two)