which corrective action should be configured or corrected for the VPN tunnel to come up properly?
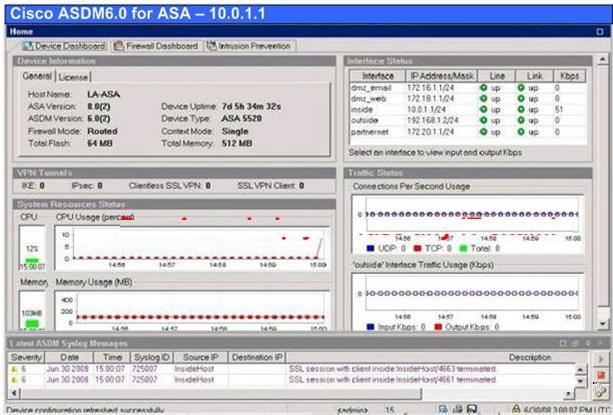
Annie is a network administrator of her company. She is responsible for a Cisco ASA security
appliance. Using a valid identity certificate from her certificate authority, she has created the
necessary configuration for remote-access VPN tunnels by use of the IPsec VPN Wizard. When
she tests the remote-access VPN, the VPN tunnel does not come up. If the remote-access VPN
configuration created by the wizard is correct and valid certificates are being used by the Cisco
ASA security appliance and Cisco VPN Client, which corrective action should be configured or
corrected for the VPN tunnel to come up properly?
What does Reverse Route Injection enable in this configuration?
Reverse route injection (RRI) is the ability for static routes to be automatically inserted into the
routing process for those networks and hosts protected by a remote tunnel endpoint. These
protected hosts and networks are known as remote proxy identities. Study the following exhibit
carefully. What does Reverse Route Injection enable in this configuration?
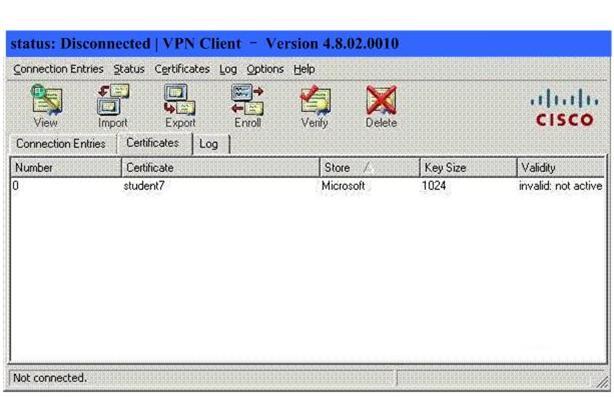
What is the reason that the certificate is in an "invalid:not active" state?
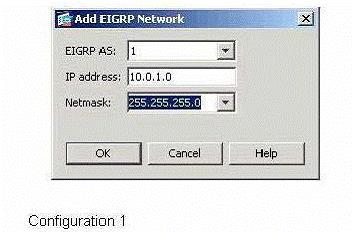
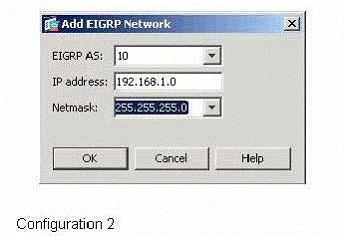
Which two Cisco ASDM configurations will add these networks to the configuration of EIGRP according to the inf
which two events will happen?
During a stateful active/standby failover, which two events will happen? (Choose two.)
Which three available Basic Host Scan checks can be configured?
Cisco Secure Desktop, an innovative feature found in Cisco’s WebVPN solutions, can help
organizations respond to government regulations for data protection by safeguarding the privacy
and security of confidential information. Afer configuring Cisco Secure Desktop on your Cisco ASA
security appliance, you should configure Cisco Secure Desktop to run Host Scan checks on the
remote endpoint. Which three available Basic Host Scan checks can be configured? (Choose
three.)
Which two options are correct about the impacts of this configuration?
Which two options are correct about the impacts of this configuration? (Choose two.)
class-map INBOUND_HTTP_TRAFFIC
match access-list TOINSIDEHOST
class-map OUTBOUND_HTTP_TRAFFIC
match access-list TOOUTSIDEHOST
policy-map MYPOLICY
class INBOUND_HTTP_TRAFFIC
inspect http
set connection conn-max 100
policy-map MYOTHERPOLICY
class OUTBOUND_HTTP_TRAFFIC
inspect http
service-policy MYOTHERPOLICY interface inside
service-policy MYPOLICY interface outside
Which three Cisco Modular Policy Framework features are bidirectional?
Modular Policy Framework provides a consistent and flexible way to configure security appliance
features in a manner similar to Cisco IOS software QoS CLI. Which three Cisco Modular Policy
Framework features are bidirectional? (Choose three.)
Which three encapsulation types will be supported by the Cisco ASA security appliance for IPsec NAT transparen
Which three encapsulation types will be supported by the Cisco ASA security appliance for IPsec
NAT transparency? (Choose three.)
Which two options are correct about the threat detection feature of the Cisco ASA adaptive security appliance?
Which two options are correct about the threat detection feature of the Cisco ASA adaptive
security appliance? (Choose two.)