Which one of the five phases of an attack attempts to become resident on a target?
Which one of the five phases of an attack attempts to become resident on a target?
Which view would you use to create a new policy within the CSA MC?
Which view would you use to create a new policy within the CSA MC?
Which operating system does not allow Query User options?
Which operating system does not allow Query User options?
Which two of the following network access rules can you use to control access to specified network services?
Which two of the following network access rules can you use to control access to specified
network services? (Choose two.)
What are three types of variables used for CSA?
What are three types of variables used for CSA? (Choose three.)
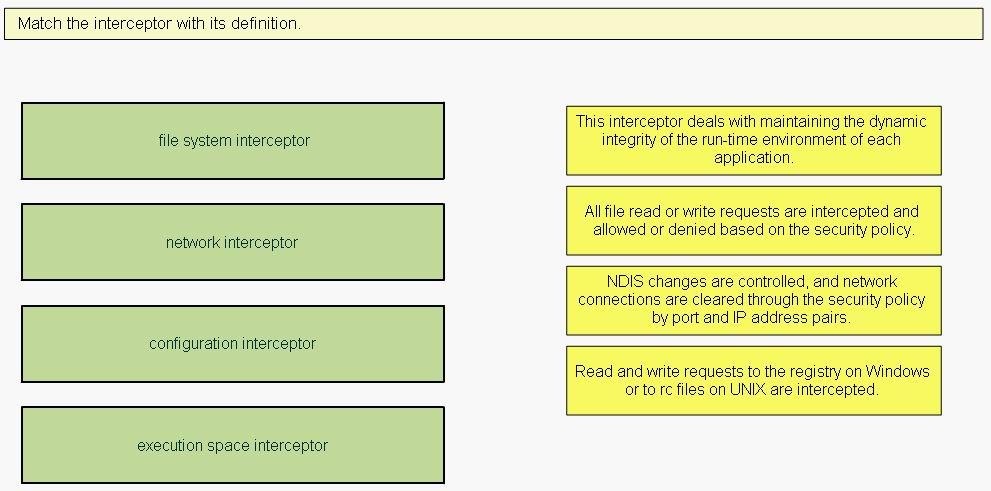
Match the interceptor with its definition.
Which port is used to access the CSA MC from the administrative workstation?
Which port is used to access the CSA MC from the administrative workstation?
Which application loads when installing the CSA MC to run the local database?
Which application loads when installing the CSA MC to run the local database?
Which view within the CSA MC allows users to see overall system status information, including a summary of rec
Which view within the CSA MC allows users to see overall system status information, including a
summary of recorded events, agent configuration, and activity?
What is the purpose of the rootkit/kernel protection rule?
What is the purpose of the rootkit/kernel protection rule?