Which statement describes a best practice when configuring trunking on a switch port?
Which statement describes a best practice when configuring trunking on a switch port?
Which type of Layer 2 attack causes a switch to flood all incoming traffic to all ports?
Which type of Layer 2 attack causes a switch to flood all incoming traffic to all ports?
What is the best way to prevent a VLAN hopping attack?
What is the best way to prevent a VLAN hopping attack?
Which statement about PVLAN Edge is true?
Which statement about PVLAN Edge is true?
which additional configuration parameter should be added to the trunking configuration?
If you are implementing VLAN trunking, which additional configuration parameter should be added
to the trunking configuration?
which type of Layer 2 attack does an attacker broadcast BDPUs with a lower switch priority?
In which type of Layer 2 attack does an attacker broadcast BDPUs with a lower switch priority?
Which security measure must you take for native VLANs on a trunk port?
Which security measure must you take for native VLANs on a trunk port?
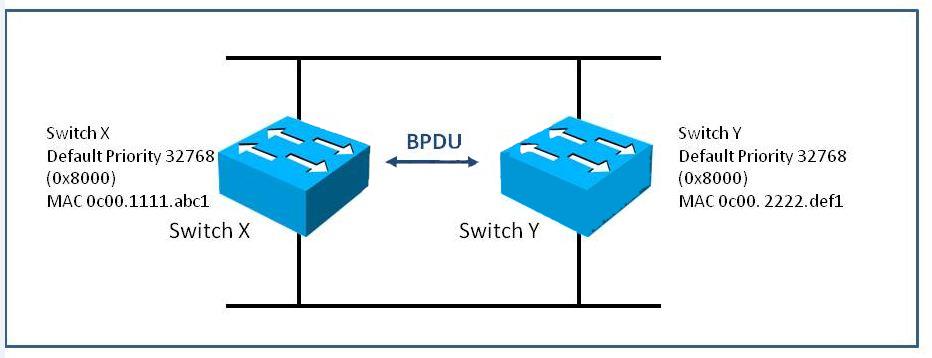
Which switch is designated as the root bridge in this topology?
what is the default action when the configured maximum number of allowed MAC addresses value is exceeded?
When port security is enabled on a Cisco Catalyst switch, what is the default action when the
configured maximum number of allowed MAC addresses value is exceeded?
Which statement best represents the characteristics of a VLAN?
Which statement best represents the characteristics of a VLAN?