Which of the following descriptions about IP spoofing is correct?
Which of the following descriptions about IP spoofing is correct?
what classification of attack?
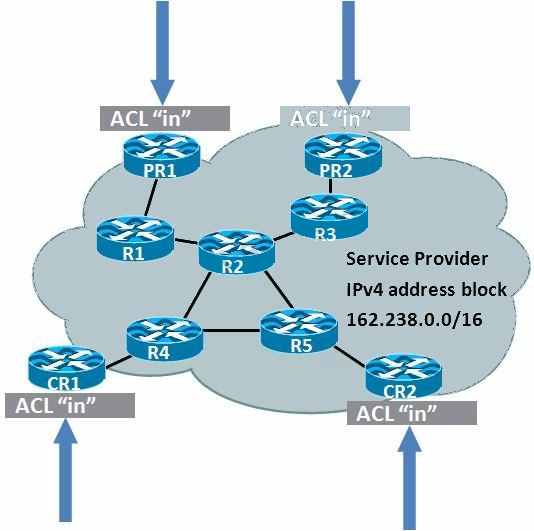
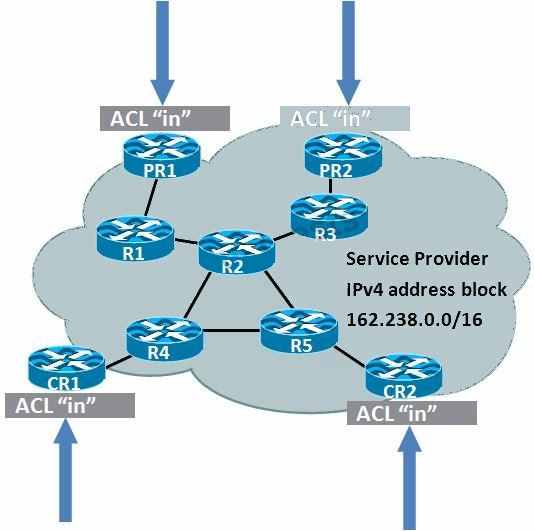
BCP (Best Common Practices) 38/RFC 2827 Ingress and Egress Packet Filtering would help
mitigate what classification of attack?
What are BCP 38 (Best Common Practices 38) / RFC 2827 Ingress Packet Filtering Principles?
What are BCP 38 (Best Common Practices 38) / RFC 2827 Ingress Packet Filtering Principles?
(Choose three.)
Which of the following IOS commands can detect whether the SQL slammer virus propagates in your networks?
Which of the following IOS commands can detect whether the SQL slammer virus propagates in
your networks?
Which two types of traffic should be permitted in the infrastructure ACL?
Which three types of traffic should be filtered in the infrastructure ACLs?
What are two uRPF working modes?
What are two uRPF working modes? (Choose two.)
Which of the following IOS features can prevent IP spoofing attacks?
Which of the following IOS features can prevent IP spoofing attacks?
What is a limitation of implementing uRPF?
What is a limitation of implementing uRPF?
Which of the following descriptions about uRPF loose mode is correct?
Which of the following descriptions about uRPF loose mode is correct? (Choose two).