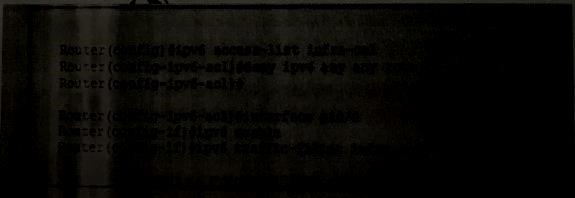
What is the effect of the given ACL policy?
Which technology builds on the vPath concept and can be used in virtual and physical environments?
Which technology builds on the vPath concept and can be used in virtual and physical
environments?
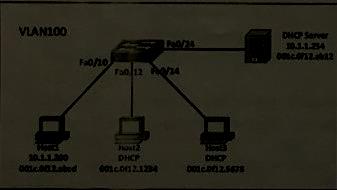
What command or command sequence must you configure on the switch to allow Host 1 to communicate with the othe
Refer to the exhibit.
Host 1 is assigned the static IP address 10.1.1.200 as shown.but host 2 and host 3 have
dynamic IP address .DHCP snooping and dynamic ARP inspection are configure on the
network.What command or command sequence must you configure on the
network.What command or command sequence must you configure on the switch to
allow Host 1 to communicate with the other hosts?
Which of the following statement is true about the ARP Spoofing attack?
Which of the following statement is true about the ARP Spoofing attack?
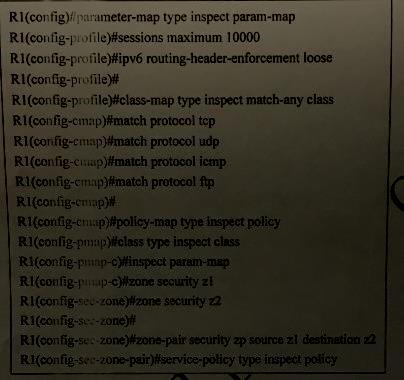
Which two statements about the given IPv6 ZBF configuration are true?
Which two statements about DTLS are true?
Which two statements about DTLS are true?(Choose two.)
What protocol does SMTPS use to secure SMTP connections?
What protocol does SMTPS use to secure SMTP connections?
What security element must an organization have in place befor it can implement a security audit and validate
What security element must an organization have in place befor it can implement a
security audit and validate the audit results?
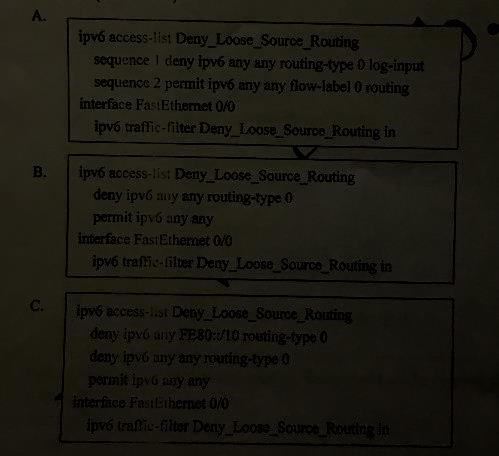
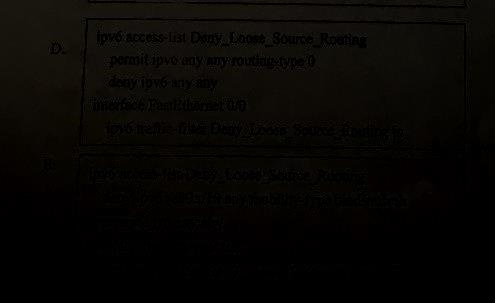
Which two router configurations block packets with the type 0 routing header on the interface?
What are three ways you can enforce a BCP38 policy on an Internet edge device?
What are three ways you can enforce a BCP38 policy on an Internet edge device?
(Choose three.)