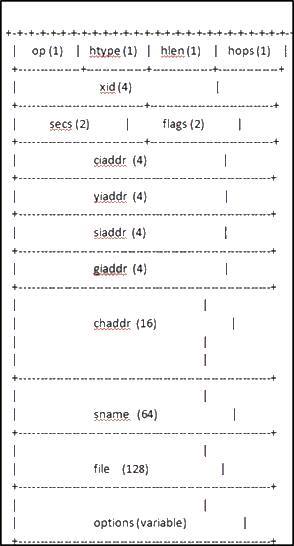
which field is populated by a DHCP relay agent with its own IP address before the DHCPDISCOVER message is forw
Which two are valid SMTP commands, according to RFC 821?
Which two are valid SMTP commands, according to RFC 821? (Choose two.)
What is the problem with EAP-MD5?
EAP-MD5 provides one-way client authentication. The server sends the client a random challenge.
The client proves its identity by hashing the challenge and its password with MD5. What is the
problem with EAP-MD5?
What are the reasons for this error?
error: % Invalid input detected at ‘^’ marker.
Above error is received when generating RSA keys for SSH access on a router using the crypto
key generate rsa command. What are the reasons for this error? (Choose two.)
Which statements apply to the above configuration?
crypto isakmp profile vpn1
vrf vpn1
keyring vpn1
match identity address 172.16.1.1 255.255.255.255
crypto map crypmap 1 ipsec-isakmp
set peer 172.16.1.1
set transform-set vpn1
set isakmp-profile vpn1
match address 101
!
interface Ethernet1/2
crypto map crypmap
Which statements apply to the above configuration? (Choose two.)
Which two statements about MACsec are true?
MACsec, which is defined in 802.1AE, provides MAC-layer encryption over wired networks. Which
two statements about MACsec are true? (Choose two.)
which type of security threat is involved?
With ASM, sources can launch attacks by sending traffic to any groups that are supported by an
active RP. Such traffic might not reach a receiver but will reach at least the first-hop router in the
path, as well as the RP, allowing limited attacks. However, if the attacking source knows a group
to which a target receiver is listening and there are no appropriate filters in place, then the
attacking source can send traffic to that group. This traffic is received as long as the attacking
source is listening to the group.
Based on the above description, which type of security threat is involved?