Which Cisco IOS feature can be used to defend against spoofing attacks?
Which Cisco IOS feature can be used to defend against spoofing attacks?
which of these statements is true?
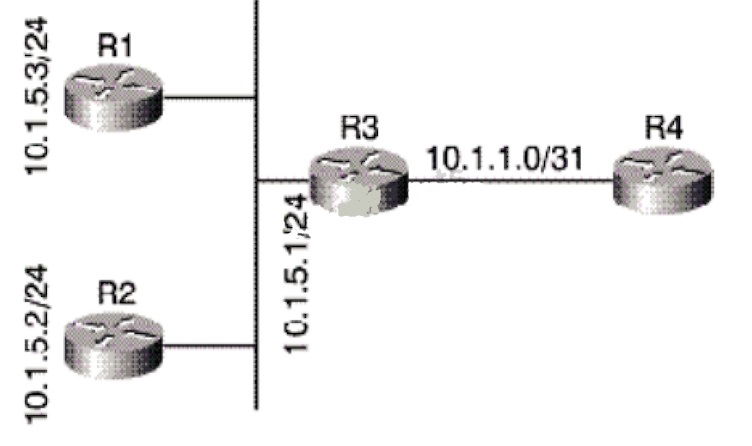
Refer to the exhibit.
Your network is primarily an OSPF network, but there are points of redistribution from other routing
protocols into your network. No route filtering has been implemented. Taking into account the
output from the show ip ospf database command in the exhibit, which of these statements is true?
What is the end result if a 10/100/1000 IEEE 802.3u Gigabit Ethernet link has autonegotiation enabled on the s
What is the end result if a 10/100/1000 IEEE 802.3u Gigabit Ethernet link has autonegotiation
enabled on the switch port and the host NIC is statically configured for 100 Mb/s and full-duplex?
what would the network (type 2) LSA generated by R3 contain?
Which of these statements correctly describes traffic policing?
Which of these statements correctly describes traffic policing?
how many links would be needed?
In order to create a fully-meshed Frame Relay network with point-to-point links between 10 sites,
how many links would be needed?
which of these problems?
If you have a large number of alignment errors, FCS errors, or late collisions, this may indicate
which of these problems?
Which three of these are reasons to implement a DMVPN using both IPsec and GRE for remote site connectivity?
Which three of these are reasons to implement a DMVPN using both IPsec and GRE for remote
site connectivity? (Choose three.)
Which of these statements correctly describes the operation of Multicast Listener Discovery?
Which of these statements correctly describes the operation of Multicast Listener Discovery?
What three types of NTP relationships form between two devices?
What three types of NTP relationships form between two devices? (Choose three.)