What type of attack did your team discover?
Your security team has discovered a malicious program that has been harvesting the CEO’s email messages and the company’s user database for the last 6
months. What type of attack did your team discover?
Which two statements regarding the ASA VPN configurations are correct?
Scenario
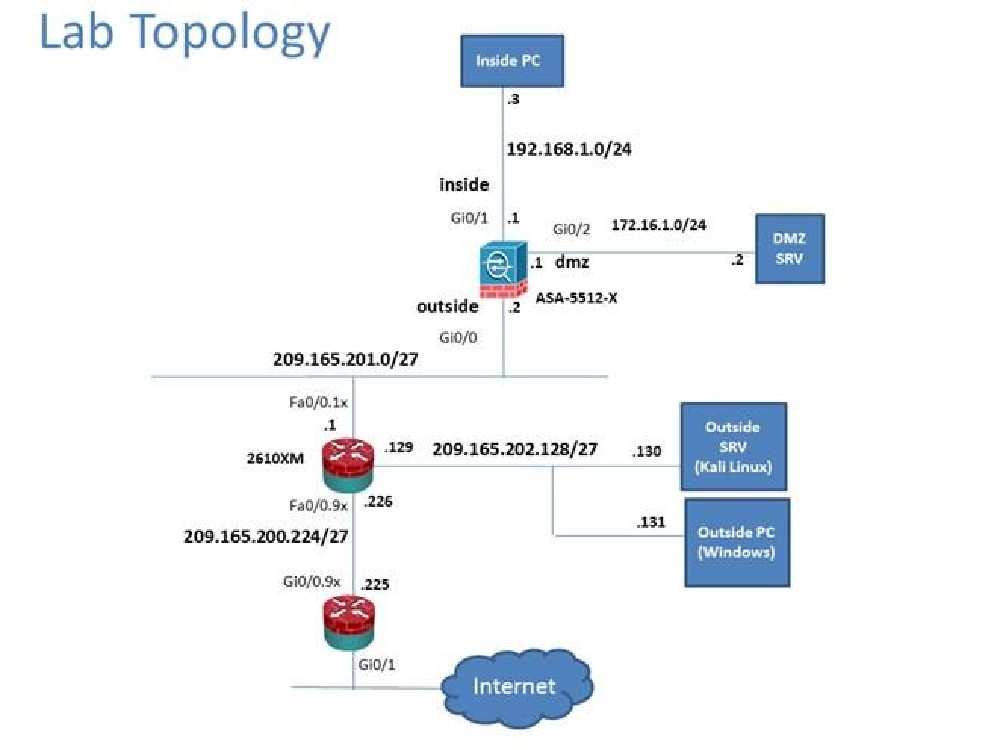
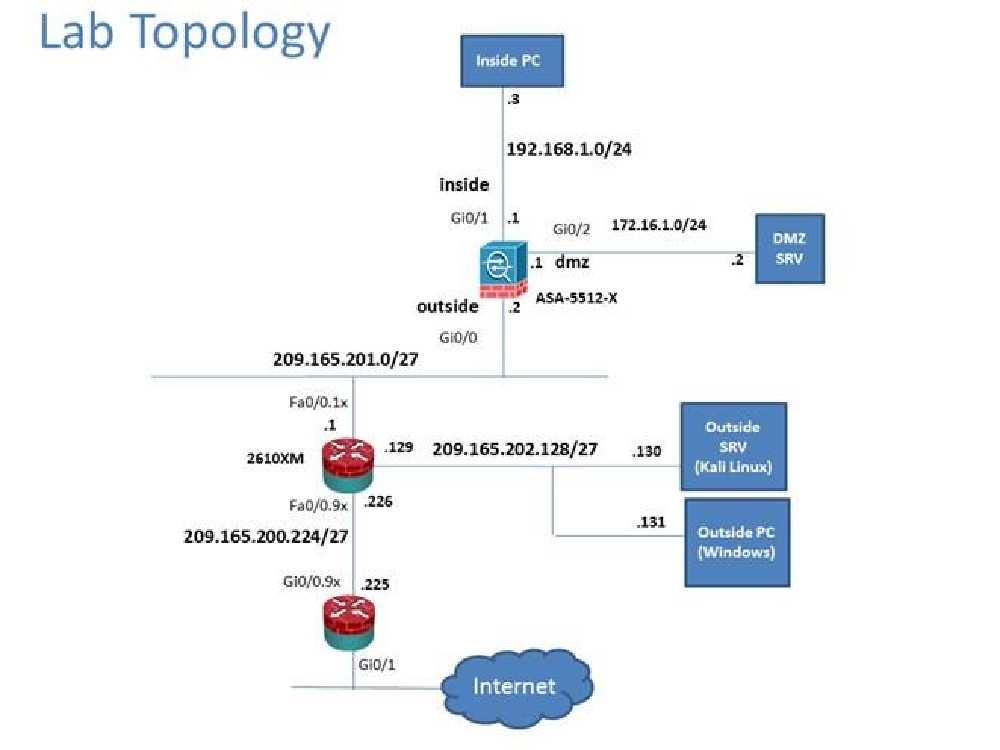
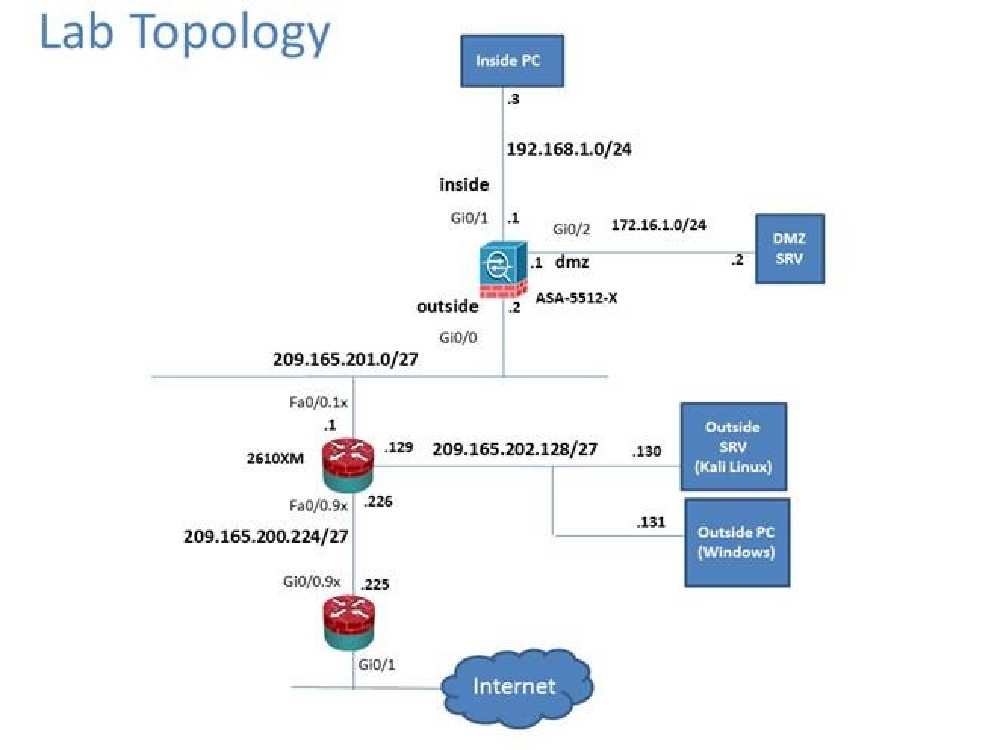
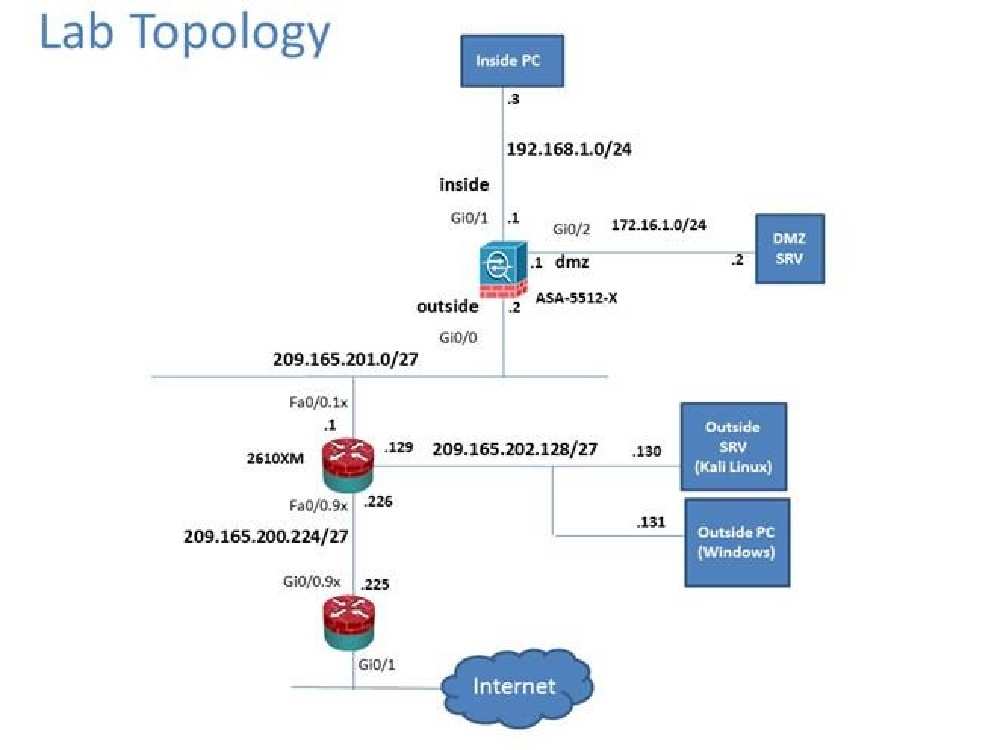
In this simulation, you have access to ASDM only. Review the various ASA configurations using ASDM then answer the five multiple choice questions about the
ASA SSLVPN configurations.
To access ASDM, click the ASA icon in the topology diagram.
Note: Not all ASDM functionalities are enabled in this simulation.
To see all the menu options available on the left navigation pane, you may also need to unexpand the expanded menu first.
Which two statements regarding the ASA VPN configurations are correct? (Choose two)
Which user authentication method is used when users login to the Clientless SSLVPN portal…?
Scenario
In this simulation, you have access to ASDM only. Review the various ASA configurations using ASDM then answer the five multiple choice questions about the
ASA SSLVPN configurations.
To access ASDM, click the ASA icon in the topology diagram.
Note: Not all ASDM functionalities are enabled in this simulation.
To see all the menu options available on the left navigation pane, you may also need to unexpand the expanded menu first.
Which user authentication method is used when users login to the Clientless SSLVPN portal using https://209.165.201.2/test?
use ASDM to accomplish the required ASA configurations to meet the requirements.
CORRECT TEXT
Scenario
Given the new additional connectivity requirements and the topology diagram, use ASDM to accomplish the required ASA configurations to meet the requirements.
New additional connectivity requirements:
Once the correct ASA configurations have been configured:
To access ASDM, click the ASA icon in the topology diagram.
To access the Firefox Browser on the Outside PC, click the Outside PC icon in the topology diagram.
To access the Command prompt on the Inside PC, click the Inside PC icon in the topology diagram.
Note:
After you make the configuration changes in ASDM, remember to click Apply to apply the configuration changes.
Not all ASDM screens are enabled in this simulation, if some screen is not enabled, try to use different methods to configure the ASA to meet the requirements.
In this simulation, some of the ASDM screens may not look and function exactly like the real ASDM.
Which four tunnelling protocols are enabled in the DfltGrpPolicy group policy?
Scenario
In this simulation, you have access to ASDM only. Review the various ASA configurations using ASDM then answer the five multiple choice questions about the
ASA SSLVPN configurations.
To access ASDM, click the ASA icon in the topology diagram.
Note: Not all ASDM functionalities are enabled in this simulation. To see all the menu options available on the left navigation pane, you may also need to unexpand
the expanded menu first.
Which four tunnelling protocols are enabled in the DfltGrpPolicy group policy? (Choose four)
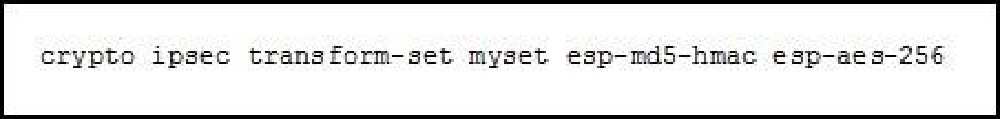
What is the effect of the given command?
Which two statements about stateless firewalls are true?
Which two statements about stateless firewalls are true? (Choose two.)
What are purposes of the Internet Key Exchange in an IPsec VPN?
What are purposes of the Internet Key Exchange in an IPsec VPN? (Choose two.)
Which actions can a promiscuous IPS take to mitigate an attack?
Which actions can a promiscuous IPS take to mitigate an attack? (Choose three.)
What are the primary attack methods of VLAN hopping?
What are the primary attack methods of VLAN hopping? (Choose two.)