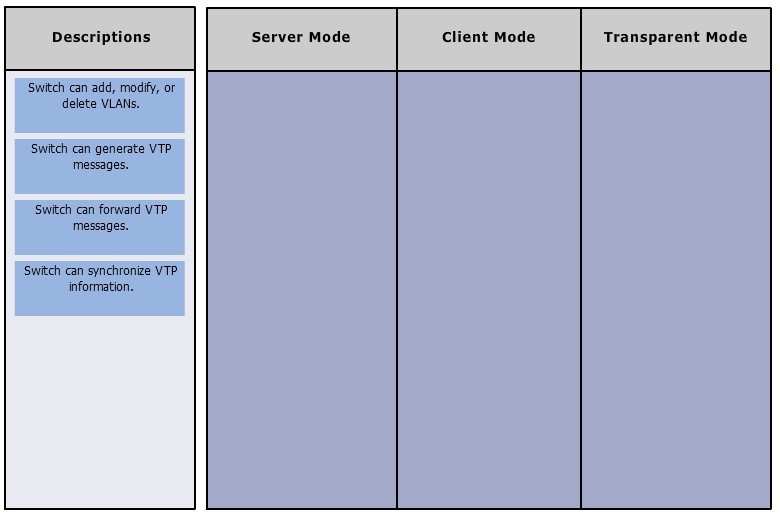
Click and drag the VLAN Trunking Protocol mode descriptions
Which of the following steps are required to prevent an…
The conference room has a switch port available for use by the presenter during classes. Each presenter uses the same PC attached to the port. You would like to
prevent any other PCs from using that port. You have completely removed the former configuration in order to start anew.
Which of the following steps are required to prevent any other PCs from using that port?
Which command is used to view the entire routing table?
Which command is used to view the entire routing table?
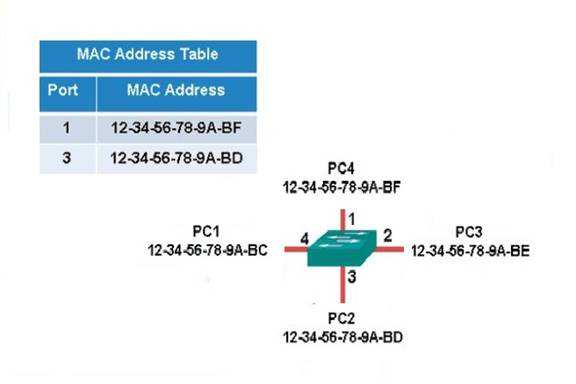
Which of the following frames will cause the switch to …
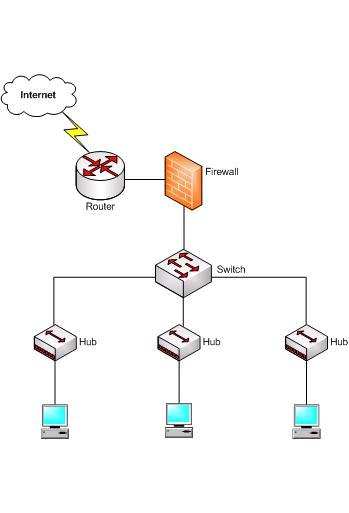
Which device in the given network diagram has as its pr…
Which Cisco IOS command enables a router to copy IOS im…
Which Cisco IOS command enables a router to copy IOS images to a router?
what would be the last legitimate host address in this …
You have been assigned a network ID of 172.16.0.0/26. If you utilize the first network resulting from this ID, what would be the last legitimate host address in this
subnet?
Which two are the limitations of the service password-e…
Which two are the limitations of the service password-encryption command? (Choose two.)
Which of the following items are NOT required to match …
Which of the following items are NOT required to match for two routers to form an OSPF adjacency?
Which command will save a dynamically learned MAC addre…
Which command will save a dynamically learned MAC address in the running-configuration of a Cisco switch?