What are three pieces of data you should review in response to a suspend SSL MITM attack?
What are three pieces of data you should review in response to a suspend SSL MITM
attack? (Choose three)
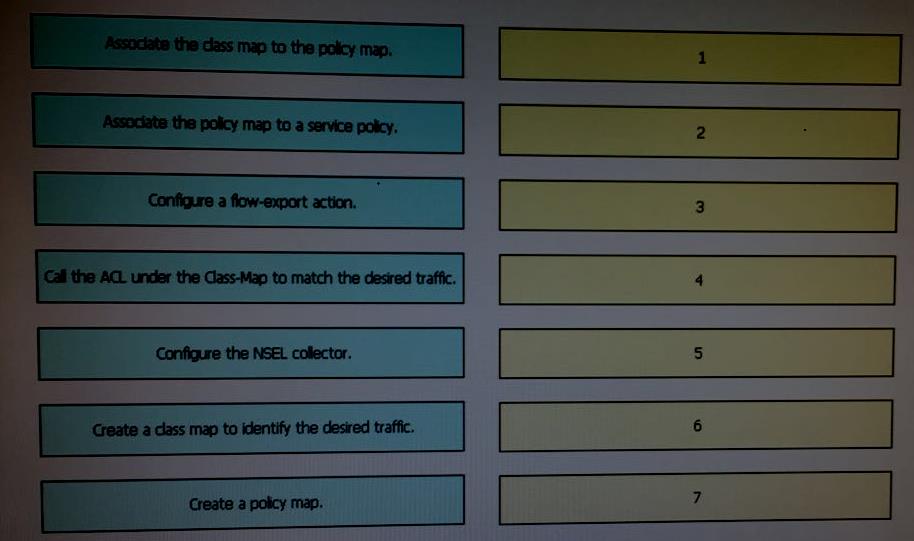
Drag each step in the configuration of a Cisco ASA NSEL export to a NetFlow collector…
Which two commands would enable secure logging on Cisco ASA to a syslog server at 10.0.0.1?
Which two commands would enable secure logging on Cisco ASA to a syslog server at
10.0.0.1? (Choose two.)
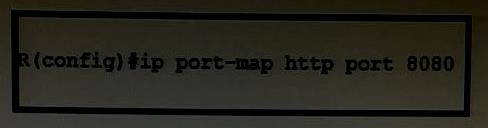
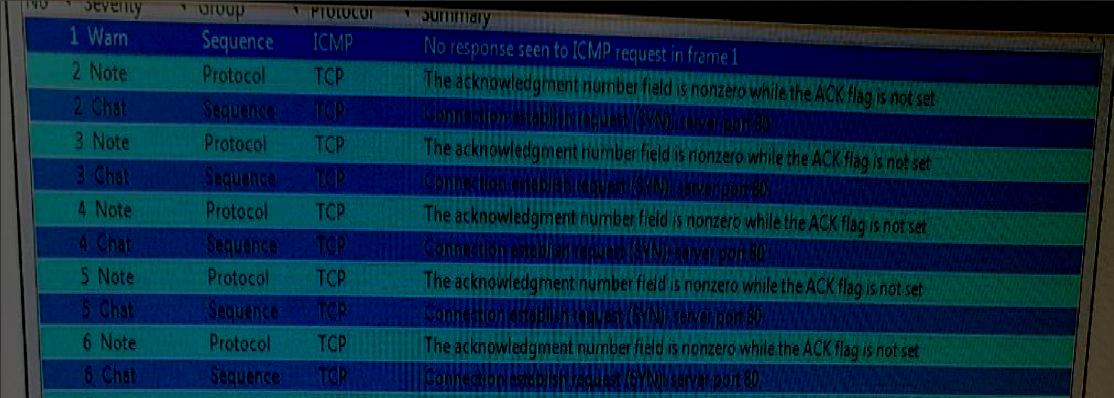
Which of the following is the correct output of the above executed command?
What protocol is responsible for issuing certificates?
What protocol is responsible for issuing certificates?
which one?
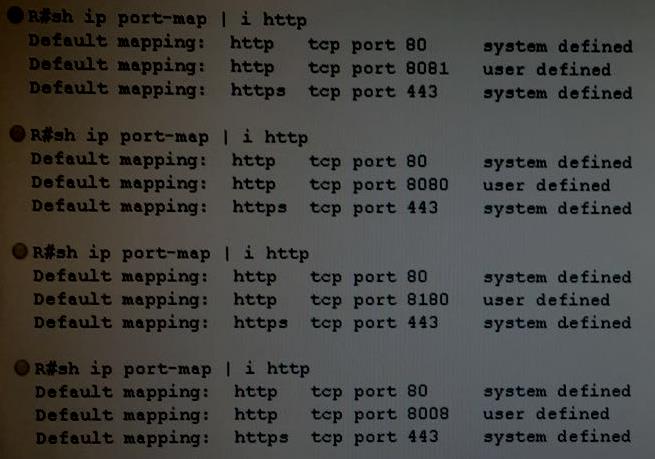
All of these are available from Cisco IPS Device Manager (Cisco IDM) except which one?
What feature on Cisco IOS router enables user identification and authorization based on per-user policies?
What feature on Cisco IOS router enables user identification and authorization based
on per-user policies?
which web policy enables failed Layer 2 authentication to fall back to WebAuth authentication with a user name
In Cisco Wireless LAN Controller (WLC) , which web policy enables failed Layer 2
authentication to fall back to WebAuth authentication with a user name and password ?