What are the three authentication methods for SIC?
What are the three authentication methods for SIC?
Which of the following is NOT a component of a Distingu…
Which of the following is NOT a component of a Distinguished Name?
Fill in the blank: With the User Directory Software Bla…
Fill in the blank: With the User Directory Software Blade, you can create R80 user definitions on a(an)
___________ Server.
Which of the following ClusterXL modes uses a non-unica…
Which of the following ClusterXL modes uses a non-unicast MAC address for the cluster IP address.
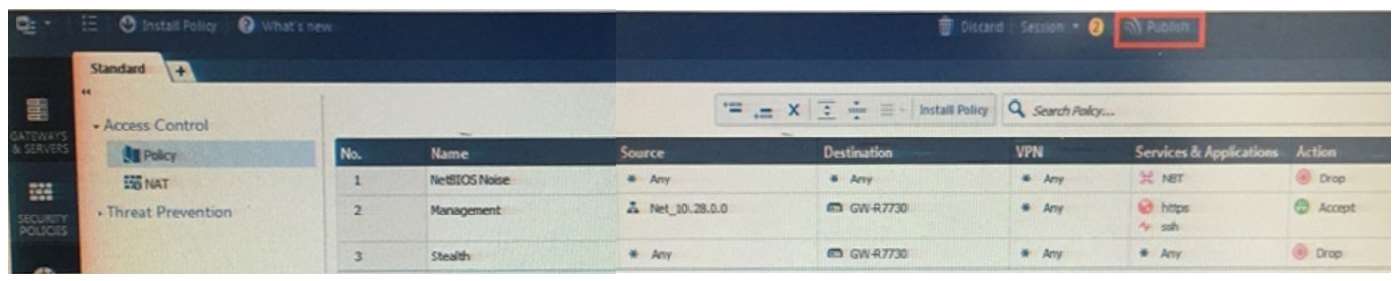
How will you describe the new “Publish” button in R80 M…
Why does it not allow him to specify the preshared secret?
An administrator is creating an IPsec site-to-site VPN between his corporate office and branch office. Both
offices are protected by Check Point Security Gateway managed by the same Security Management Server.
While configuring the VPN community to specify the pre-shared secret the administrator found that the check
box to enable pre-shared secret is shared and cannot be enabled. Why does it not allow him to specify the preshared secret?
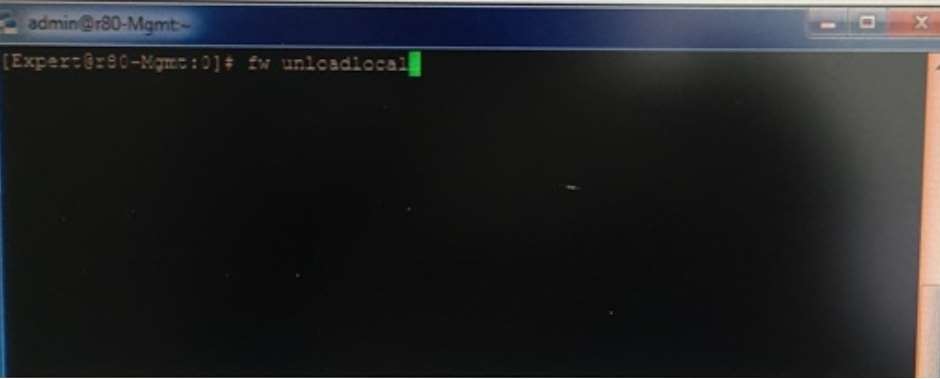
What will be the effect of running the following comman…
Which product correlates logs and detects security thre…
Which product correlates logs and detects security threats, providing a centralized display of potential attack
patterns from all network devices?
Which VPN routing option uses VPN routing for every con…
Which VPN routing option uses VPN routing for every connection a satellite gateway handles?
Which utility allows you to configure the DHCP service …
Which utility allows you to configure the DHCP service on GAIA from the command line?