which of the following problems?
The fw monitor utility is used to troubleshoot which of the following problems?
which of the following objects?
NAT can NOT be configured on which of the following objects?
which Security Gateways have licenses that will expire …
Your bank’s distributed R77 installation has Security Gateways up for renewal. Which SmartConsole application
will tell you which Security Gateways have licenses that will expire within the next 30 days?
What CLI utility allows an administrator to capture tra…
What CLI utility allows an administrator to capture traffic along the firewall inspection chain?
Which statement below is TRUE about these types of comm…
Mesh and Star are two types of VPN topologies. Which statement below is TRUE about these types of
communities?
What statement is true regarding Visitor Mode?
What statement is true regarding Visitor Mode?
Which of these components does NOT require a Security G…
Which of these components does NOT require a Security Gateway R77 license?
What is the reason for this behavior?
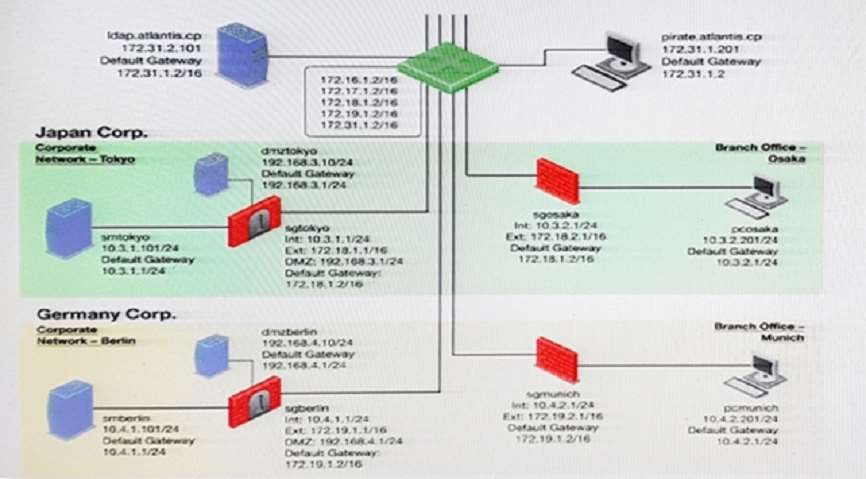
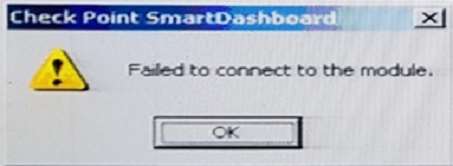
You want to reset SIC between smberlin and sgosaka.
In SmartDashboard, you choose sgosaka, Communication, Reset. On sgosaka, you start cpconfig,
choose Secure Internal Communication and enter the new SIC Activation Key. The screen reads The SIC
was successfully initialized and jumps back to the menu. When trying to establish a connection, instead of a
working connection, you receive this error message:
What is the reason for this behavior?
What is the correct order for pushing SIC certificates …
You installed Security Management Server on a computer using GAiA in the MegaCorp home office. You use
IP address 10.1.1.1. You also installed the Security Gateway on a second GAiA computer, which you plan to
ship to another Administrator at a MegaCorp hub office. What is the correct order for pushing SIC certificates to
the Gateway before shipping it?
1. Run cpconfig on the Gateway, select Secure Internal Communication, enter the activation key, and
reconfirm.
2. Initialize Internal Certificate Authority (ICA) on the Security Management Server.
3. Configure the Gateway object with the host name and IP addresses for the remote site.
4. Click the Communication button in the Gateway object’s General screen, enter the activation key, and click
Initialize and OK.
5. Install the Security Policy.
Which of the following is NOT defined by an Access Role…
Which of the following is NOT defined by an Access Role object?