For standard RFC (Request for Comments) complaint IKE VPN’s, a user’s authentication method should
For standard RFC (Request for Comments) complaint IKE VPN’s, a user’s authentication method
should be defined where?
Receivers then authenticate senders’ public keys, by matching the CA public keys to the CA private keys
The following steps correctly list the actions taken by a Certificate Authority (CA)
1. Users send their public keys to a CA in a secure manner.
2. The CA signs the public keys with its own private keys, creating CA public keys.
3. The CA creates a certificate with its public and private keys.
Receivers then authenticate senders’ public keys, by matching the CA public keys to the CA
private keys on the certificates.
Which of the following will cause VPN-1/Firewall-1 to reset TCP connections with a server protected by SYNDefe
With Secure Client, if you have more than one network adapter: (Choose all that apply)
With Secure Client, if you have more than one network adapter: (Choose all that apply)
Which load-balancing method chooses the physical server closest to the client, based on DNS?
Which load-balancing method chooses the physical server closest to the client, based on DNS?
which the following operating systems does Check Point support installation of the VPN-1/Firewall-1 Management
On which the following operating systems does Check Point support installation of the VPN-1/Firewall-1 Management Server?
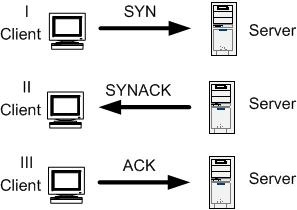
SYN flood attacks are used in the Denial-of-Service (Dos) attacks, or in conjunction with other exploits to bl
SYN flood attacks are used in the Denial-of-Service (Dos) attacks, or in conjunction with other
exploits to block access to a server network.
Which command is used to export a group of users from VPN-1/Firewall?
Which command is used to export a group of users from VPN-1/Firewall?
Which of the following lists the most likely cause of the problem, and the appropriate remedy?
You are using Hybrid IKE. SecuRemote produces the error “Certificate is badly signed”. Which of
the following lists the most likely cause of the problem, and the appropriate remedy?
If you do not configure any groups during Solaris installation, ONLY the Super-User will be able to access and
If you do not configure any groups during Solaris installation, ONLY the Super-User will be able to
access and execute the VPN-1/Firewall-1 Module.