Why could OpenVMS Mail be considered a security risk?
Why could OpenVMS Mail be considered a security risk?
Which two object classes can have audit events applied to them?
Which two object classes can have audit events applied to them? Select two.
what files a process currently has open across all disk volumes?
On a system with user file activity across several volumes, which command or utility can a system
manager use to determine what files a process currently has open across all disk volumes?
What two items should be included in an organization’s Configuration Management records?
What two items should be included in an organization’s Configuration Management records?
Select two.
Which two are the correct descriptions for L and P when discussing a device protection mask (RWLP)?
Which two are the correct descriptions for L and P when discussing a device protection mask
(RWLP)? Select two.
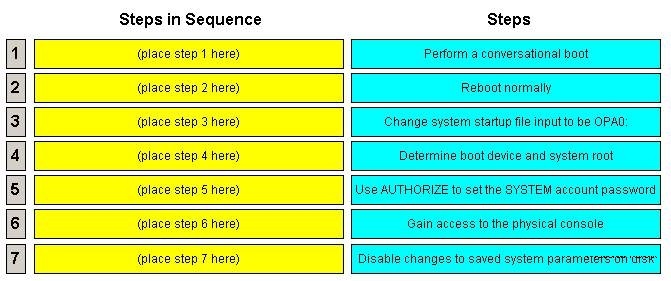
You need to break into a system when none of the accounts or passwords are known
what happens to system activity if the audit server’s log destination runs out of disk space?
By default, what happens to system activity if the audit server’s log destination runs out of disk
space?
Why could this happen?
The DCL command DIR 0:: fails with the error message %SYSTEM-F-LINKEXIT, network partner
exited. Why could this happen?
What are two of the vulnerabilities that are introduced?
A backup system disk copy is missing. What are two of the vulnerabilities that are introduced?
Select two.
What is the purpose of "high water marking"?
What is the purpose of “high water marking”?