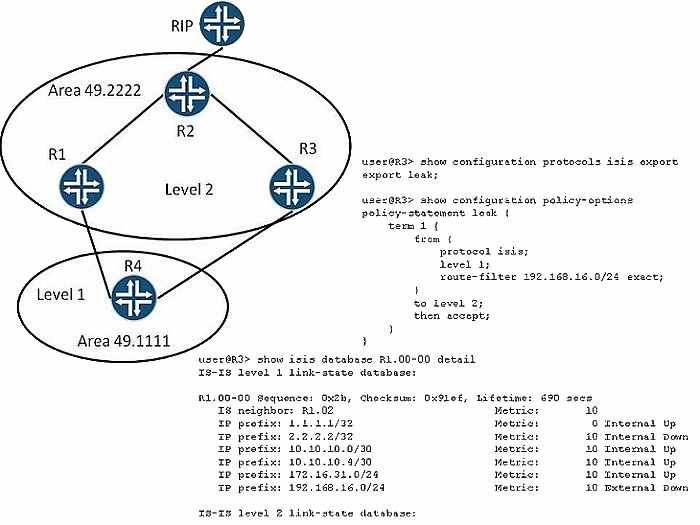
Why does R3’s route leaking policy appear not to be working?
Refer to the Exhibit.
In the exhibit, R2 is receiving external routing information for the 192.168.16.0/24 prefix and is
redistributing it into IS-IS. R1 has a policy that leaks the 192.168.16.0/24 route into Area 49.1111.
R3 has a policy that leaks the 192.168.16.0/24 route into Area 49.2222. However, the IS-IS
version of the route does not appear in R2’s routing table.
Why does R3’s route leaking policy appear not to be working?
Which two actions accomplish the task?
— Exhibit –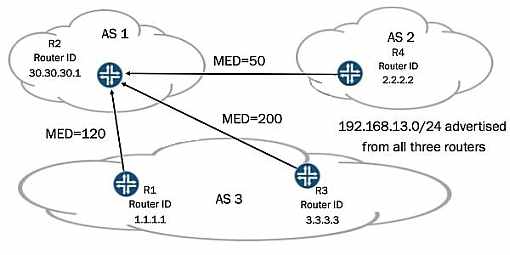
— Exhibit —
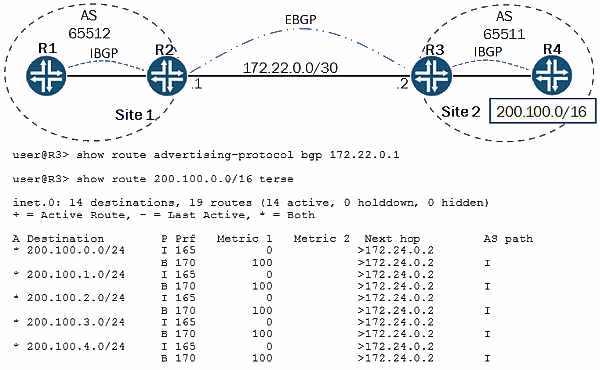
Refer to the Exhibit.
You administer the network shown in the exhibit. Routers R1, R3, and R4 are sending the same
prefix to R2. All routers are using default local-preference values. You must make the prefix from
R4 the most preferred.
Which two actions accomplish the task? (Choose two.)
Why is this happening?
Which two actions will accomplish this task?
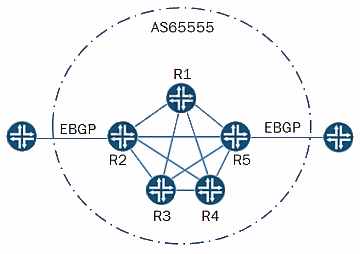
Refer to the Exhibit.
Referring to the exhibit, routers R1 through R5 exist in a fully-meshed IBGP group. You want the
routes received through EBGP on R1 to be advertised to the EBGP peer connected to R5. You
want the routes received through EBGP on R5 to be installed on R1; however, you do not want the
those routes to be advertised to the EBGP peer connected to R1.
Which two actions will accomplish this task? (Choose two.)
What would cause this behavior?
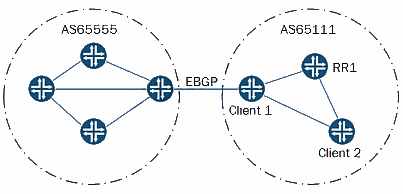
Refer to the Exhibit.
The Client 1 router forwards a route learned from its EBGP peer to the route reflector RR1. The
route reflector forwards the route to the Client 2 router. However, the Client 2 router uses
suboptimal routing to reach the EBGP route destination.
What would cause this behavior?
which policy statement action for the export policy on A2 will perform this task?
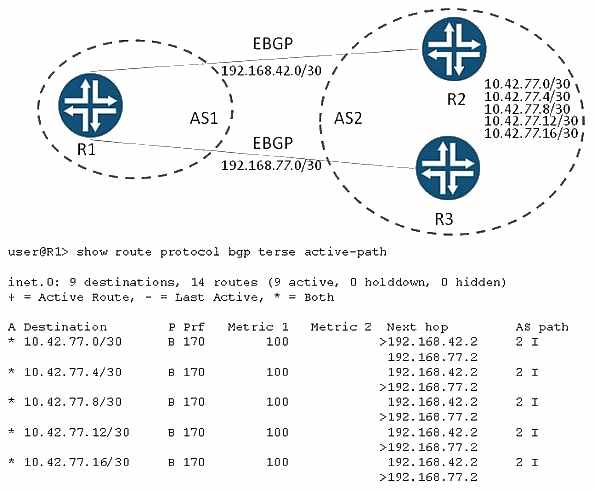
Which configuration parameter would create a routing table as shown in the exhibit?
Which method should you use?
Refer to the Exhibit.
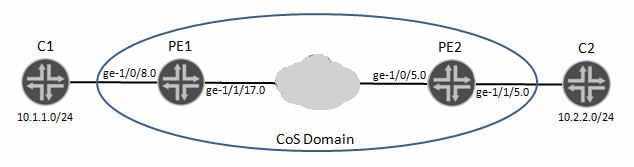
Referring to the exhibit, you must ensure that all traffic sourced from C1 and destined to C2 is
associated with the expedited forwarding class. Also, you must ensure that all other traffic not
sourced from C1 is not impacted by the identified modification.
Which method should you use?
which LSP will be preempted by LSP5?
— Exhibit –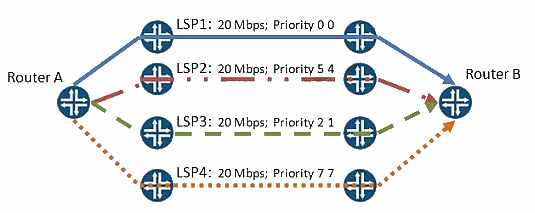
— Exhibit —
Refer to the Exhibit.
Your network has multiple LSPs between Router A and Router B, as shown in the exhibit. You add
a new LSP between these routers with the following parameters:
LSP5: 20 Mbps; Priority 4 3
Assuming no link has 20 Mbps available, which LSP will be preempted by LSP5?
which LSPs are candidates for preemption by LSP5?
— Exhibit –
— Exhibit —
Refer to the Exhibit.
Your network has multiple LSPs between Router A and Router B, as shown in the exhibit. You add
a new LSP between these routers with the following parameters:
LSP5: 20 Mbps; Priority 2 2
Assuming no link has 20 Mbps available, which LSPs are candidates for preemption by LSP5?
(Choose two.)