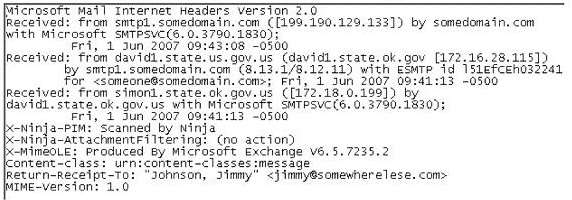
where did the email first originate from?
What will the following command accomplish in Linux?
What will the following command accomplish in Linux?
fdisk /dev/hda
What would this attack on the company PBX system be called?
Cylie is investigating a network breach at a state organization in Florida. She discovers that the intruders were
able to gain access into the company firewalls by overloading them with IP packets. Cylie then discovers
through her investigation that the intruders hacked into the company phone system and used the hard drives
on their PBX system to store shared music files. What would this attack on the company PBX system be
called?
What type of analysis helps to identify the time and se…
What type of analysis helps to identify the time and sequence of events in an investigation?
What is the first step taken in an investigation for la…
What is the first step taken in an investigation for laboratory forensic staff members?
What encryption technology is used on Blackberry device…
What encryption technology is used on Blackberry devices Password Keeper?
Which program is the bootloader when Windows XP starts up?
Which program is the bootloader when Windows XP starts up?
what proprietary RIM-operated mechanism?
All Blackberry email is eventually sent and received through what proprietary RIM-operated mechanism?
Where are files temporarily written in Unix when printing?
Where are files temporarily written in Unix when printing?
what layer of the OSI model?
Sniffers that place NICs in promiscuous mode work at what layer of the OSI model?