Which three of these are required in order to set up a CSC SSM on the Cisco ASA?
Which three of these are required in order to set up a CSC SSM on the Cisco ASA? (Choose three.)
Which command will redirect HTTP traffic bound for the DMZ web server to its real IP address of 10.10.11.4?
An internet user is sending HTTP traffic to a DMZ server with the external address of 192.168.1.4. Which command will redirect HTTP traffic bound for the DMZ web server to its real IP address of 10.10.11.4?
Which of these commands displays the status of the CSC SSM on the Cisco ASA?
Which of these commands displays the status of the CSC SSM on the Cisco ASA?
Which of these commands must be used when configuring advanced FTP inspection, such as FTP banner masking or t
Which of these commands must be used when configuring advanced FTP inspection, such as FTP banner masking or the blocking of specific usernames?
Which three of the these are mandatory for accomplishing this goal with your Cisco ASA?
You want to block a new instant messaging application. Which three of the these are mandatory for accomplishing this goal with your Cisco ASA? (Choose three.)
What do these commands accomplish?
Which of these statements regarding Active/Active failover configurations is correct?
Which of these statements regarding Active/Active failover configurations is correct?
Which two tasks do these commands accomplish?
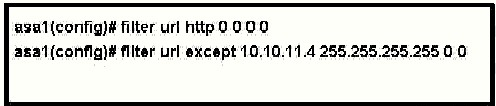
Refer to the exhibit. The adaptive security appliance administrator needs to filter a single website on a host with the IP address 10.10.11.4, but allow access to all other websites. The administrator enters the commands shown and then executes them.
Which two tasks do these commands accomplish? (Choose two.)
Which command will provide interface IP information, the interface operational status, and the interface confi
Which command will provide interface IP information, the interface operational status, and the interface configuration method for an adaptive security appliance?
Which three of these commands, used individually, would allow the administrator to place limits on the number
An administrator wants to protect a DMZ web server from SYN flood attacks. Which three of these commands, used individually, would allow the administrator to place limits on the number of embryonic connections? (Choose three.)