What happens?
which use case is a basic or standard access control list (ACL) appropriate?
For which use case is a basic or standard access control list (ACL) appropriate?
When should the administrator accept the upgrade?
A network administrator is completing an In-Service Software Upgrade (ISSU) for an Intelligent
Resilient Framework (IRF) virtual devices. The device has two members. Each member has one
management module. Member1 is currently the master. The administrator has initiated a rollback
time for this upgrade.
When should the administrator accept the upgrade?
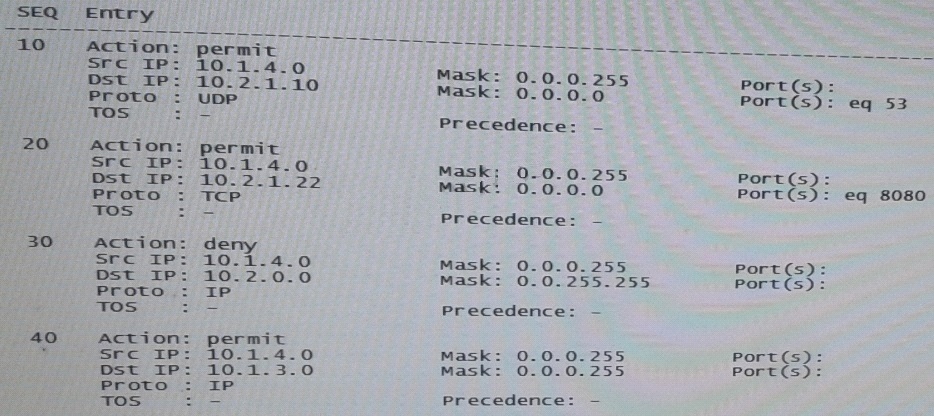
Match each characteristic to the connect multicast routing protocol.
Which statement correctly describes UAM support for this requirement?
A company is determining whether HP IMC User Access manager (UAM) meets its needs for a
RADIUS server. The company requires a solution for dynamic access control lists based on user
identity and location (connected switch ID). Which statement correctly describes UAM support for
this requirement?
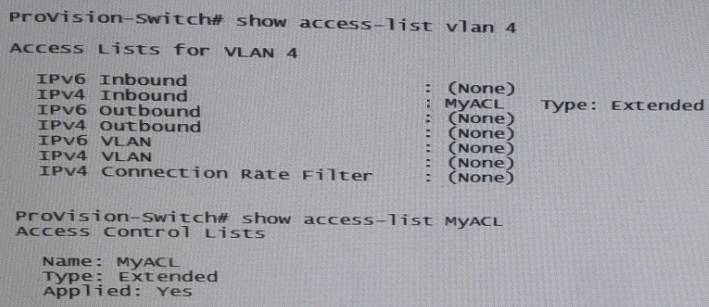
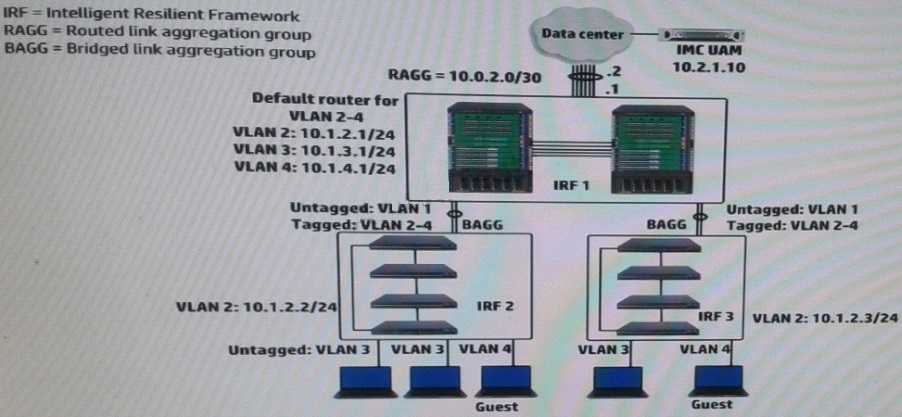
Where should the network administrator enable portal authentication?
A company wants to implement a portal authentication solution for guests (such a solution is also
called Web-Auth). Guest belong to VLAN4, as shown in the exhibit. The intelligent Management
Center (IMC) User Access Manager (UAM) will provide authentication and the Web Portal.
Where should the network administrator enable portal authentication?
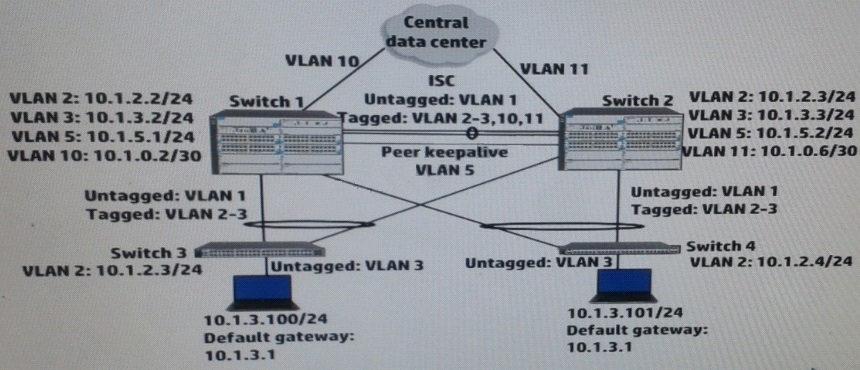
How can a network administrator increase the resiliency of this solution?
Switch 1 and switch 2 run open Shortest Path First (OSPF) on all VLANs. Both switches establish
an OSPF adjacency to a router at the main data center. Exhibit shows shoes some virtual Routing
Redundancy Protocol (VRRP) and OSPF settings on Switch 1 during normal operation.
How can a network administrator increase the resiliency of this solution?
which additional step must the administrator complete to accomplish this?
A network administrator wants to configure Open Shortest Path (OSPF) MD5 authentication on
VLAN 100 on an HP ProVision switch. The administrator has created a global MD5 key chain with
an ID and key string that matches the neighbor’s. which additional step must the administrator
complete to accomplish this?
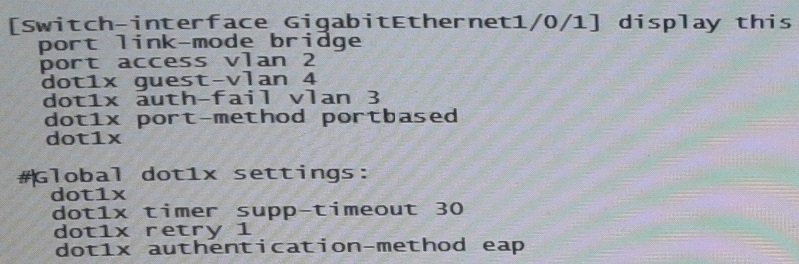
How does the switch port handle the client?
How does administrator configure UAM to apply the correct setting?
A company uses 802.1X authentication to force users to connect to the network. The company
uses access layer switches to enforce the 802.1X authentication and HP IMC User Access
manager (UAM) as the RADIUS server.
The customer requires switches to apply a specific settings to contractor use connections. The
network administrator checks the switch documentation and determines that this settings uses a
vendor-specific attribute (VSA). The administrator check UAN and verifies that it has this VSA
defined on it.
How does administrator configure UAM to apply the correct setting?